Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How do I edit this regex for proper field extr...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Having issues getting field extraction on Cisco ASA lines to work consistently without getting invalid information. Field extraction generates the following regex:
"^(?:[^ \n]* ){8}(?P<ASAMSGCODE>[^:]+)"
The events that are skewed report the value as CDT. When the field extraction is performed on this set of events, the regex is:
"^(?:[^ \n]* ){9}(?P<ASAMSGCODE>[^:]+)"
It appears to be counting spaces. The example where {8} is has a single space between the Aug and the 10, where the {9} has a double space between the Aug and the 9. I have attempted several manipulations on the regex without success.
Example where {8}
Aug 10 11:07:10 #.#.#.# :Aug 10 11:07:10 CDT: %ASA-session-4-106023: Deny icmp src devicename:#.#.#.# dst inside:devicename (type 8, code 0) by access-group "aclname" [0x0, 0x0]
Example where {9}
Aug 9 23:59:58 #.#.#.# :Aug 09 23:59:59 CDT: %ASA-session-4-106023: Deny tcp src devicename dst outside:devicename by access-group "aclname" [0x0, 0x0]
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The automatic field extractor leaves something to be desired. Using your sample data and regex101.com, this seems to work.
(?P<ASAMSGCODE>%ASA[^:]+)
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Based on your log sample, you want to extract value %ASA-session-4-106023 and it's always prefix by CDT:. If this is correct, just try this.
CDT:\s*(?P<ASAMSGCODE>[^:]+)
A sample runanywhere query with your sample data which used for testing.
| gentimes start=-1 | eval temp="Aug 10 11:07:10 #.#.#.# :Aug 10 11:07:10 CDT: %ASA-session-4-106023: Deny icmp src devicename:#.#.#.# dst inside:devicename (type 8, code 0) by access-group \"aclname\" [0x0, 0x0]$Aug 9 23:59:58 #.#.#.# :Aug 09 23:59:59 CDT: %ASA-session-4-106023: Deny tcp src devicename dst outside:devicename by access-group \"aclname\" [0x0, 0x0]" | table temp | makemv temp delim="$" | mvexpand temp | rename temp as _raw | rex "CDT:\s*(?P<ASAMSGCODE>[^:]+)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The automatic field extractor leaves something to be desired. Using your sample data and regex101.com, this seems to work.
(?P<ASAMSGCODE>%ASA[^:]+)
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Worked like a champ.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What exactly are you trying to extract? Do you want whatever is where the # sign is in your example?
You could use a \s+? to capture either a single or double space.. Give me a line or two of exactly what you want extracted
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
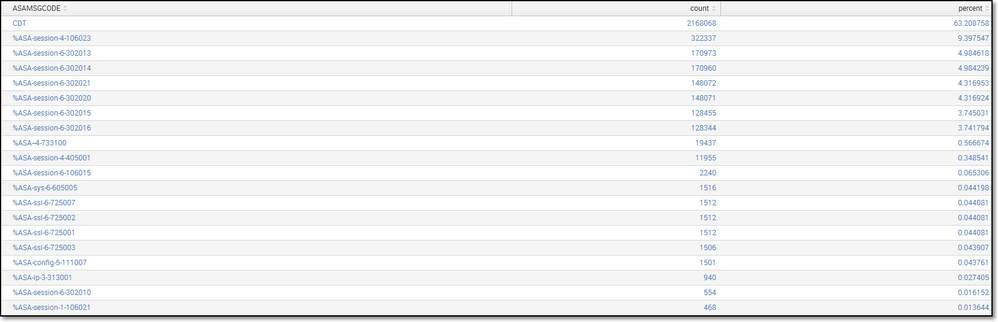
I am looking to extract the ASA message code values (ex. %ASA-session-4-106023) to generate table like the original attached image. The #'s were numbers that I sanitized from the log line.