Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- regex help!
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
kiran331
Builder
06-12-2017
07:45 PM
How to extract the IP OR hostname from the field "source"?
source=/opt/var/log/splunk/ciscoasa/11.12.22.345/2017_06_05_21_cisco.log
source=/opt/var/log/splunk/ciscoasa/abc_xyz/2017_06_05_21_cisco.log
I need to extract 11.12.22.345 & abc_xyz
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
06-12-2017
07:58 PM
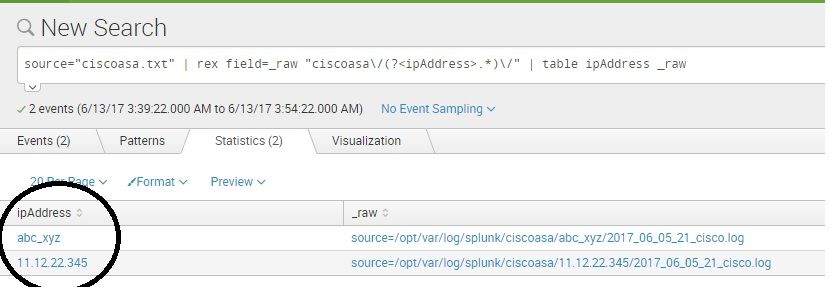
Hi Kiran, Verified and this works fine -
source="ciscoasa.txt" | rex field=_raw "ciscoasa\/(?<ipAddress>.*)\/" | table ipAddress _raw
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
horsefez
Motivator
06-13-2017
05:46 AM
Hi,
because I was bored I made this redundant answer.
yoursearch | rex field=source "(?<host>[^\/]+)\/[^\/]+(?:$)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
gcusello

SplunkTrust
06-12-2017
11:26 PM
Hi kiran331,
Try this:
your_search | rex field=source "ciscoasa\/(?<host>[^\/]*)" | ...
you can test it at https://regex101.com/r/wrL9Ze/1
Bye.
giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
06-12-2017
07:58 PM
Hi Kiran, Verified and this works fine -
source="ciscoasa.txt" | rex field=_raw "ciscoasa\/(?<ipAddress>.*)\/" | table ipAddress _raw
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Observability Simplified: Combining User Experience, Application Performance & ...
Tech Talk
Observability Simplified: Combining User Experience, Application Performance & Network ...
Event Series May & June: From Network Visibility to Service Intelligence
Unifying the Network: Moving from Alert Noise to Service Intelligence with Splunk ITSI
In today’s hybrid ...
Global Splunk User Group Events: May + June 2026
Your Splunk Community Awaits: Discover Upcoming User Group Events Worldwide
Staying ahead in the fast-paced ...