Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: regex help!
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
kiran331
Builder
06-12-2017
07:45 PM
How to extract the IP OR hostname from the field "source"?
source=/opt/var/log/splunk/ciscoasa/11.12.22.345/2017_06_05_21_cisco.log
source=/opt/var/log/splunk/ciscoasa/abc_xyz/2017_06_05_21_cisco.log
I need to extract 11.12.22.345 & abc_xyz
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
06-12-2017
07:58 PM
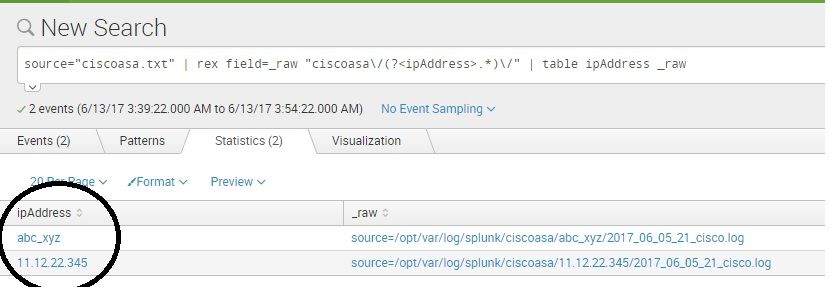
Hi Kiran, Verified and this works fine -
source="ciscoasa.txt" | rex field=_raw "ciscoasa\/(?<ipAddress>.*)\/" | table ipAddress _raw
thanks and best regards,
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
horsefez
Motivator
06-13-2017
05:46 AM
Hi,
because I was bored I made this redundant answer.
yoursearch | rex field=source "(?<host>[^\/]+)\/[^\/]+(?:$)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
gcusello

SplunkTrust
06-12-2017
11:26 PM
Hi kiran331,
Try this:
your_search | rex field=source "ciscoasa\/(?<host>[^\/]*)" | ...
you can test it at https://regex101.com/r/wrL9Ze/1
Bye.
giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
06-12-2017
07:58 PM
Hi Kiran, Verified and this works fine -
source="ciscoasa.txt" | rex field=_raw "ciscoasa\/(?<ipAddress>.*)\/" | table ipAddress _raw
thanks and best regards,
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
Get Updates on the Splunk Community!
AI for AppInspect
We’re excited to announce two new updates to AppInspect designed to save you time and make the app approval ...
App Platform's 2025 Year in Review: A Year of Innovation, Growth, and Community
As we step into 2026, it’s the perfect moment to reflect on what an extraordinary year 2025 was for the Splunk ...
Operationalizing Entity Risk Score with Enterprise Security 8.3+
Overview
Enterprise Security 8.3 introduces a powerful new feature called “Entity Risk Scoring” (ERS) for ...