Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Splunk eval if with wildcard
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sboogaar
Path Finder
01-31-2019
05:41 AM
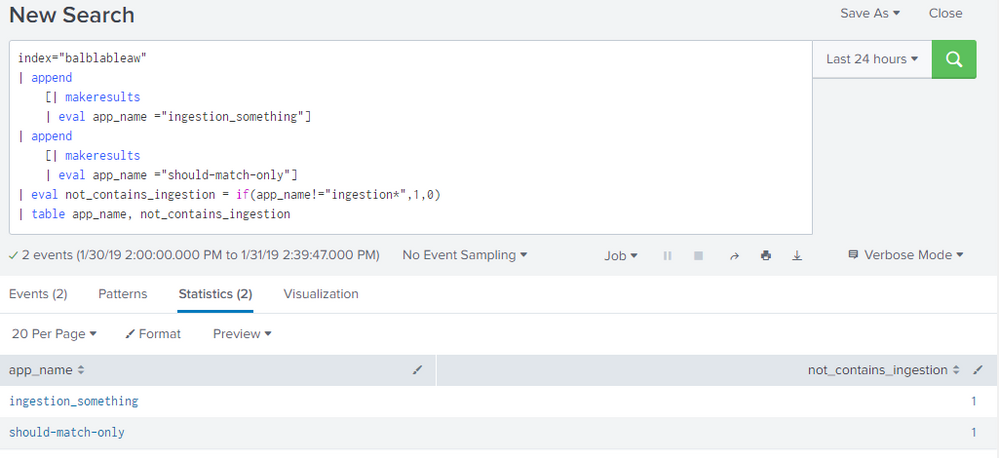
Im trying to set a boolean based on a match in a string.
I want to set a value to 1 if it does not match ingestion* and set it to 0 if it does match.
The following example shows the problem:
index="balblableaw"
| append
[| makeresults
| eval app_name ="ingestion_something"]
| append
[| makeresults
| eval app_name ="should-match-only"]
| eval not_contains_ingestion = if(app_name!="ingestion*",1,0)
| table app_name, not_contains_ingestion
The expected result was that should-match-only would be 1 and the ingestion_something would be 0
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
renjith_nair
Legend
01-31-2019
05:45 AM
@sboogaar,
Use match
index="balblableaw"
| append
[| makeresults
| eval app_name ="ingestion_something"]
| append
[| makeresults
| eval app_name ="should-match-only"]
| eval not_contains_ingestion = if(match(app_name,"ingestion"),0,1)
| table app_name, not_contains_ingestion
---
What goes around comes around. If it helps, hit it with Karma 🙂
What goes around comes around. If it helps, hit it with Karma 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vishaltaneja070
Motivator
01-31-2019
05:47 AM
Try this:
index="balblableaw"
| append
[| makeresults
| eval app_name ="ingestion_something"]
| append
[| makeresults
| eval app_name ="should-match-only"]
| eval not_contains_ingestion = if(app_name like "ingestion%" ,1,0)
| table app_name, not_contains_ingestion
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
renjith_nair
Legend
01-31-2019
05:45 AM
@sboogaar,
Use match
index="balblableaw"
| append
[| makeresults
| eval app_name ="ingestion_something"]
| append
[| makeresults
| eval app_name ="should-match-only"]
| eval not_contains_ingestion = if(match(app_name,"ingestion"),0,1)
| table app_name, not_contains_ingestion
---
What goes around comes around. If it helps, hit it with Karma 🙂
What goes around comes around. If it helps, hit it with Karma 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sboogaar
Path Finder
02-01-2019
04:30 AM
Thanks for the answer, can you explain why my own example was not working. I try to understand the disabilities from splunk.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
renjith_nair
Legend
02-02-2019
05:00 AM
In eval it doesn't treat * as wildcard but as literal
---
What goes around comes around. If it helps, hit it with Karma 🙂
What goes around comes around. If it helps, hit it with Karma 🙂
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Tech Talk Recap | Mastering Threat Hunting
Mastering Threat HuntingDive into the world of threat hunting, exploring the key differences between ...
Observability for AI Applications: Troubleshooting Latency
If you’re working with proprietary company data, you’re probably going to have a locally hosted LLM or many ...
Splunk AI Assistant for SPL vs. ChatGPT: Which One is Better?
In the age of AI, every tool promises to make our lives easier. From summarizing content to writing code, ...