Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to separate out basic search of Splunk in two ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to separate out basic search of Splunk in two different columns?
AjayTakur
Loves-to-Learn Everything
04-26-2023
12:34 PM
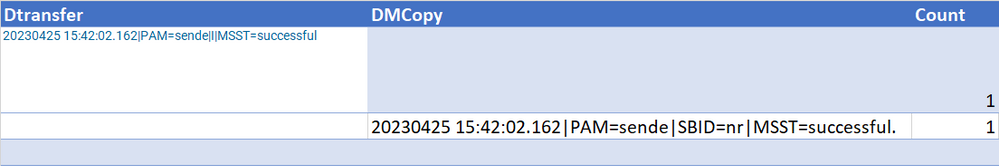
I am new to Splunk and facing an issue in separating out the two columns of the query. I tried with the below query and found the results as shown below in table1
...| append [search index="pd" "successful" "notif/output/" | stats count by _raw |fields count | rename _raw as Dtransfer] | append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count by _raw |fields count | rename _raw as DMCopy]
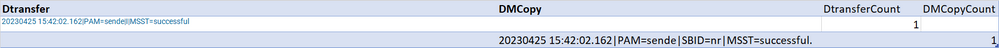
How do I achieve the expected result shown in Table 2? I need to display two separate columns DtransferCount and DMCopyCount
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
04-26-2023
01:09 PM
Specify the name of the count field in the stats commands.
...|
append [search index="pd" "successful" "notif/output/" | stats count as DtransferCount by _raw |fields DtransferCount | rename _raw as Dtransfer] |
append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count as DDMCopyCount by _raw |fields DDMCopyCount | rename _raw as DMCopy]
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Cisco Live 2026 is almost here, and this ...
What Is the Name of the USB Key Inserted by Bob Smith? (BOTS Hint, Not the Answer)
Hello Splunkers,
So you searched, “what is the name of the usb key inserted by bob smith?”
Not gonna lie… ...
Automating Threat Operations and Threat Hunting with Recorded Future
Automating Threat Operations and Threat Hunting
with Recorded Future
June 29, 2026 | Register
Is your ...