Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How to separate out basic search of splunk in ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to separate out basic search of Splunk in two different columns?
AjayTakur
Loves-to-Learn Everything
04-26-2023
12:34 PM
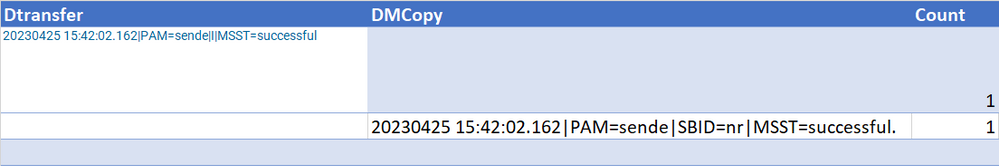
I am new to Splunk and facing an issue in separating out the two columns of the query. I tried with the below query and found the results as shown below in table1
...| append [search index="pd" "successful" "notif/output/" | stats count by _raw |fields count | rename _raw as Dtransfer] | append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count by _raw |fields count | rename _raw as DMCopy]
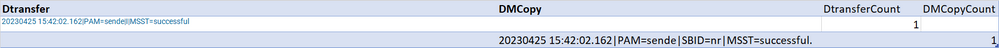
How do I achieve the expected result shown in Table 2? I need to display two separate columns DtransferCount and DMCopyCount
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
04-26-2023
01:09 PM
Specify the name of the count field in the stats commands.
...|
append [search index="pd" "successful" "notif/output/" | stats count as DtransferCount by _raw |fields DtransferCount | rename _raw as Dtransfer] |
append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count as DDMCopyCount by _raw |fields DDMCopyCount | rename _raw as DMCopy]
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Tech Talk Recap | Mastering Threat Hunting
Mastering Threat HuntingDive into the world of threat hunting, exploring the key differences between ...
Observability for AI Applications: Troubleshooting Latency
If you’re working with proprietary company data, you’re probably going to have a locally hosted LLM or many ...
Splunk AI Assistant for SPL vs. ChatGPT: Which One is Better?
In the age of AI, every tool promises to make our lives easier. From summarizing content to writing code, ...