Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Splunk Add-on for Netflow: Why are Netflow timesta...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
We are collecting some test flows from a Cisco ASA, in order to evaluate the feasibility of implementing this app across our entire environment.
We were able to get the app working without any issues, and the search head sees the flows without any issues.
The problem that we are having is that Splunk Enterprise seems to be interpreting the timestamp on a flow, incorrectly.
For example, the raw flow in the nfdump-ascii directory looks like this -
2015-06-01 16:36:31,2015-06-01 16:36:31,0.000,10.0.0.115,30.30.30.30,49649,443,TCP,......,0,0,0,0,0,0,8,7,0,0,0,0,0,0,0.0.0.0,0.0.0.0,0,0,00:00:00:00:00:00,00:00:00:00:0:00,00:00:00:00:00:00,00:00:00:00:00:00,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0,0-0-0, 0.000, 0.000, 0.000,10.10.0.10,0/0,1,2015-06-01 16:36:32.088
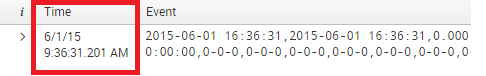
When I see the flow in the Splunk UI, it shows up thusly -
Any idea on what could be wrong ?
Thanks and Regards,
Madan Sudhindra
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
this can be affected by a lot of different settings; the best way to figure out what's going on is to open a support ticket.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Madan,
Can you let me know how you configured the netflow? Did you configure the script using root user? We are not able to see any netflow data in ascii directory?
Thanks
Hemendra
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am using port 2056 to receive V9 netflow data.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
this can be affected by a lot of different settings; the best way to figure out what's going on is to open a support ticket.