Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Table command does not display field with spaces w...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello All,
I have a search query that performs lookups against a CSV file and outputs only those hosts that are in the CSV file.
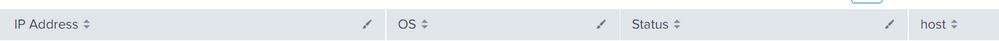
The CSV file has the following 4 columns and notice the IP Address column has a white space in it.
I have verified the following command displays the values correctly of all hosts with their IP in a table
| inputlookup linux_servers.csv | table host "IP Address"
Now, if put the same thing in a tstats command, it does not show any results. Any ideas why does it not take "IP Address" even though i have stated double quotes ??
| tstats max(_time) as lastSeen_epoch WHERE index=linux [| inputlookup linux_servers.csv | table host "IP Address" ] by host
The following search works fine , if i take out the "IP Address" . It displays the table with host column.
| tstats max(_time) as lastSeen_epoch WHERE index=linux [| inputlookup linux_servers.csv | table host ] by host
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When troubleshooting a query containing a subsearch, it helps to run the subsearch by itself with the | format command appended. This will show exactly what is added to the main search.
| inputlookup linux_servers.csv | table host "IP Address" | formatYou'll find the main search ends up looking something like this
| tstats max(_time) as lastSeen_epoch WHERE index=linux ((host=foo AND "IP Address"=1.1.1.1) OR (host=bar AND "IP Address"=1.2.3.4)) by hostMake sure that final query string makes sense with your data.
What you're more likely running into, however, is one of the fields in the tstats command is not indexed and so it is not found. The "IP Address" field is the most likely candidate.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When troubleshooting a query containing a subsearch, it helps to run the subsearch by itself with the | format command appended. This will show exactly what is added to the main search.
| inputlookup linux_servers.csv | table host "IP Address" | formatYou'll find the main search ends up looking something like this
| tstats max(_time) as lastSeen_epoch WHERE index=linux ((host=foo AND "IP Address"=1.1.1.1) OR (host=bar AND "IP Address"=1.2.3.4)) by hostMake sure that final query string makes sense with your data.
What you're more likely running into, however, is one of the fields in the tstats command is not indexed and so it is not found. The "IP Address" field is the most likely candidate.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are right. Very basic mistake to forget that "IP Address" field is not indexed . Tstats would never find this field.