Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Splunk search does not return event data when ther...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have a created a splunk alert when there is a failure occurs. I have query as follows:
index=* source=*** |spath path=TestLog.TestFailureLog.appName output=APPNAME|spath path=TestLog.TestFailureLog.eventType output=EVENTTYPE|spath path=TestLog.TestFailureLog.payload.level output=LEVEL|spath path=TestLog.TestFailureLog.payload.failureCount output=FAILURECOUNT|spath path=TestLog.TestFailureLog.payload.errorDescription output=ERRORDESCRIPTION|where APPNAME!="" and LEVEL="ERROR"|table APPNAME,EVENTTYPE,LEVEL,FAILURECOUNT,ERRORDESCRIPTION
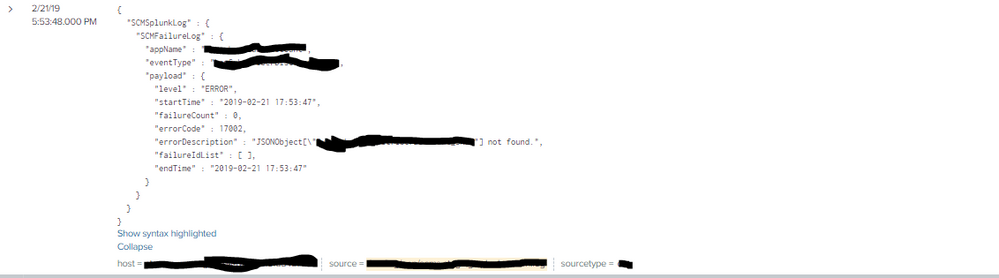
It is working fine when I have single jsonobject per event in the log . For eg:
If I have Data like below:
But, if in case I have both success and failure log in the same event, that particular event is vomited and it returns all the remaining failure logs.
Can Anyone please suggest me the solution for it.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@karthi25
Can you please try below search? I have split events as expected. For that, I have added || using replace tp split events. Here Might be you need to change values}\n{ to your_brackates.
<<YOUR_host_source_sourcetype>>
| fields _time _raw
| eval data = replace(_raw,"}\n{","}||{")
| eval data = split(data,"||")
| mvexpand data | eval _raw=data | kv | table TestSplunkLog.*
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@karthi25
Can you please try below search? I have split events as expected. For that, I have added || using replace tp split events. Here Might be you need to change values}\n{ to your_brackates.
<<YOUR_host_source_sourcetype>>
| fields _time _raw
| eval data = replace(_raw,"}\n{","}||{")
| eval data = split(data,"||")
| mvexpand data | eval _raw=data | kv | table TestSplunkLog.*
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@kamlesh_vaghela finally it works, Thanks a lot.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@karthi25
Great.
Please upvote and accept this answer to close this question.
Happy Splunking
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@karthi25
It seems your given JSON is invalid. Can you please share actual event having multiple logs? Don't beautify JSON share it as it is.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@kamlesh_vaghela Thanks for your response.I have updated my question. Please look in to it. Kindly let me know, if you found anything. Since, these logs are from other sources, I can't change the logging format .
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, @karthi25 for updating question. Is it ok if you share 2nd event in text format? So we can work on those samples to help you. Use Code Sample ( 5th icon in above panel) for same. update confidential values with a dummy value.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@kamlesh_vaghela Sure. Please find the text format for the 2nd event below:
{
"TestSplunkLog" : {
"TestSuccessLog" : {
"appName" : "Testsscount",
"eventType" : "event1",
"payload" : {
"level" : "INFO",
"startTime" : "2019-02-21 18:02:58",
"sourceCount" : 0,
"successCount" : 0,
"duplicateCount" : 0,
"publishedCount" : 0,
"endTime" : "2019-02-21 18:02:59"
}
}
}
}
{
"TestSplunkLog" : {
"TestFailureLog" : {
"appName" : "Testsscount",
"eventType" : "event1",
"payload" : {
"level" : "ERROR",
"startTime" : "2019-02-21 18:02:58",
"failureCount" : 0,
"errorCode" : 17002,
"errorDescription" : "IO Error: Unknown host specified ",
"failureIdList" : [ ],
"endTime" : "2019-02-21 18:02:59"
}
}
}
}
Collapse
host = *** source =*** sourcetype =***