Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Line chart of daily event totals over N-days
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Line chart of daily event totals over N-days
scotmatson
Explorer
01-22-2019
07:16 AM
I need to display trending IP events over the course of 90 days with each day being a sum of the events.
My original query which was only interested in daily metrics on a more granular level uses stats > sort > addcoltotal. I need to retain the sorting behavior as I am only interested in the top-20 IPs currently. I've been able to get the daily totals I am interested in but I am not sure how to repeat the query across the 90 days and translate that into a timechart.
... base
| fields ip email username inf ssr
| stats count(ip) as ar count(ssr) as ssre count(eval(inf)) as ssby count(eval(inf="success")) as ls count(eval(inf="warning")) as lf dc(eval(coalesce(email, username))) as ua by ip
| sort 20 -ar
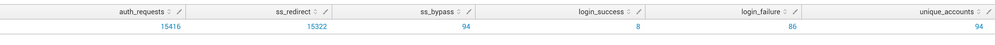
| stats sum(ar) as auth_requests sum(ssre) as ss_redirect sum(ssby) as ss_bypass sum(ls) as login_success sum(lf) as login_failure sum(ua) as unique_accounts
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Community Content Calendar, September edition
Welcome to another insightful post from our Community Content Calendar! We're thrilled to continue bringing ...
Splunkbase Unveils New App Listing Management Public Preview
Splunkbase Unveils New App Listing Management Public PreviewWe're thrilled to announce the public preview of ...
Leveraging Automated Threat Analysis Across the Splunk Ecosystem
Are you leveraging automation to its fullest potential in your threat detection strategy?Our upcoming Security ...