Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- If I use more than 6 times append command in query...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nivethainspire_
Explorer
10-28-2020
06:51 AM
I ran the below query,
index=s sourcetype=S_1
| search Gene="dow" OR Gene="x" OR Gene="ari" OR Gene="lia" OR Gene="SX" OR Gene=z
| append [search index=s sourcetype="S_2"|fillnull |eval Gene="rage"]
| append [search index=s sourcetype=S_3 |fillnull|eval Gene="ork"]
| append [search index=s sourcetype=S_4|fillnull|eval Gene="tat"]
| append [search index=s sourcetype=S_5 | fillnull |eval Gene="bas"]
| append [search index=s sourcetype=S_6 | fillnull |eval Gene="bas1"]
| append [search index=s sourcetype=S_7|fillnull value=""|eval Gene="App"|fields *]
|rename Gene as General
| stats count by General,"Report"
|eventstats sum(*) as sum_* by General
|foreach * [eval "Status %"=round((count/sum_count)*100,2)]|rename count as Count
|fields - sum_count
|chart values("Status %") over "Report" by General
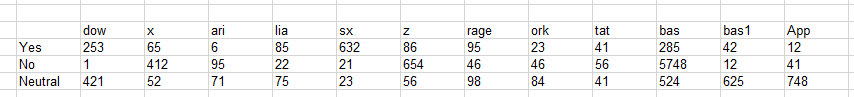
|sort "Report" descI expect the below Result,
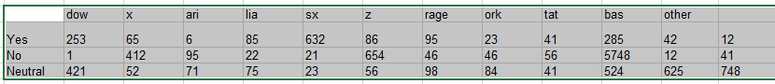
But I get the below result, where "bas1" and "App" shows together as "OTHER"
And it happens after I use the chart command.
Anyone can help me out.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
10-29-2020
01:42 AM
useother=f just drop that OTHER column away. If you want to see it, then you should add limit=0 (to see all) or limit=20 (to see 20 values).
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
10-28-2020
07:17 AM
It's not the number of appends, it's the number of fields. By default, the chart command displays 10 fields and puts the rest into "other". To change that, use "| chart useother=f ...".
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nivethainspire_
Explorer
10-29-2020
01:30 AM
@richgalloway Still I face the same issue.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
10-29-2020
01:42 AM
useother=f just drop that OTHER column away. If you want to see it, then you should add limit=0 (to see all) or limit=20 (to see 20 values).
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
10-28-2020
07:10 AM
Hi
this is due to chart's limit which is 10 by default. You could change it by adding chart limit=XX (or limit=0 to unlimited it).
Anyhow you probably should tune your search to use eg. stat and not append? There are good presentation in conf how to do it.
https://conf.splunk.com/files/2020/slides/TRU1761C.pdf
r. Ismo
this is due to chart's limit which is 10 by default. You could change it by adding chart limit=XX (or limit=0 to unlimited it).
Anyhow you probably should tune your search to use eg. stat and not append? There are good presentation in conf how to do it.
https://conf.splunk.com/files/2020/slides/TRU1761C.pdf
r. Ismo
Get Updates on the Splunk Community!
Data Management Digest – December 2025
Welcome to the December edition of Data Management Digest!
As we continue our journey of data innovation, the ...
Index This | What is broken 80% of the time by February?
December 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...
Unlock Faster Time-to-Value on Edge and Ingest Processor with New SPL2 Pipeline ...
Hello Splunk Community,
We're thrilled to share an exciting update that will help you manage your data more ...