Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to extract the field with regex
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
danielwan
Explorer
09-25-2017
06:42 PM
I would like to extract the field of "/home/y/conf/video_dir.conf" with regex when the event contains "critical" keyword (there are some other state keywords like "normal", "debug")
2011-01-01 01:49:00 UTC [ critical] [ PID=14154][ GENERAL] File /home/y/conf/video_dir.conf doesn't exist or not readable.
I ran '... | rex field=_raw "^.critical.*File\s+(?)\s+.$" but it's not working. Any advice on making it work?
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
09-25-2017
11:48 PM
Please try -
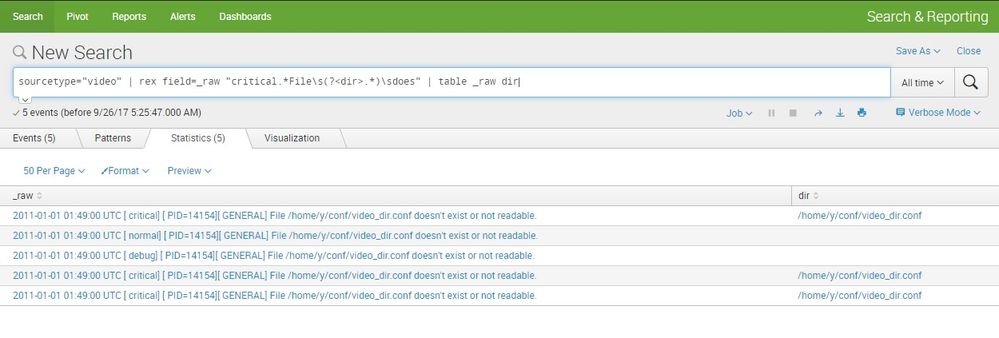
sourcetype="video" | rex field=_raw "critical.*File\s(?<dir>.*)\sdoes" | table _raw dir
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
09-25-2017
11:48 PM
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Cisco Live 2026 is almost here, and this ...
What Is the Name of the USB Key Inserted by Bob Smith? (BOTS Hint, Not the Answer)
Hello Splunkers,
So you searched, “what is the name of the usb key inserted by bob smith?”
Not gonna lie… ...
Automating Threat Operations and Threat Hunting with Recorded Future
Automating Threat Operations and Threat Hunting
with Recorded Future
June 29, 2026 | Register
Is your ...