Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How to extract source and destination IP field...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to extract source and destination IP fields?
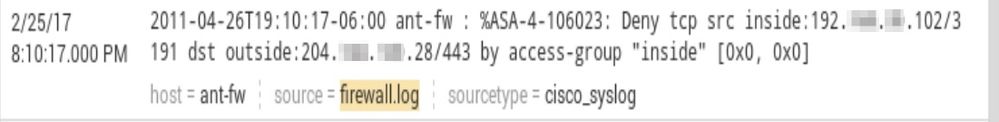
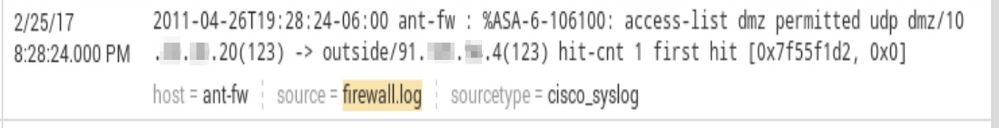
I am trying to configure various search fields for a firewall log from the field extractor but Splunk is pulling up some incorrect results. Any help would be appreciated. The two images are examples of the logs.
Here is the expression that incorrectly pulls up some results.
^[^/\n]*/(?P[^\(]+)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
First Extraction: https://regex101.com/r/CFOb1y/1
Second Extraction: https://regex101.com/r/43d4OA/1
Obviously, if you provide a full log, I could help more, but this should get you started.
Also, check this out: https://docs.splunk.com/Documentation/Splunk/6.5.2/SearchReference/Scrub
And if you want a CIM compliant TA for Cisco ASA, I would try: https://splunkbase.splunk.com/app/1620/
Odds are, the Splunk extractions are better.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What results are you getting and what do you expect?
A copy-and-paste of the event text is more helpful than a screen shot.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As richgalloway mentioned copy past would be usefull. By the title I assume you are looking for the source and destination fields.
For your first example inside:(?<src_ip>[^\/]+)\/(?<src_port>\d+) dst outside:(?<dest_ip>[^\/]+)\/(?<dest_port>\d+) might be a fitting regex.
something something ... deny tcp src inside:123.123.123.123/444 dst outside:111.222.333.444/555 ....
I personally would go with another extraction for your other example since both events are not quite similar but I'm sure someone else would combine both.
For the second example permitted \w+ \w+\/(?<src_ip>[^\(]+)\(\w+\) -> outside\/(?<dest_ip>[^\(]+) might fit.
something something ... permitted udp dmz/111.222.333.444(123) -> outside/123.123.123.123(123) ....