Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How do you discard specific fields and keep th...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How do you discard specific fields and keep the rest?
Hi All,
Could you please let me know how to discard specific fields and keep the rest while indexing in Splunk ?
like
field 1=a
field 2 =b
field 3 = c
field 4 =d
Fields 1-3 have to be discarded and only field 4 needs to be shown in Splunk events /_raw
Thanks
Rakesh Singh
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So you just want to strip of that timestamp part? I'm a little curious as to why, but still, try this in props.conf:
[kafka:topicEvent]
SEDCMD-striptimestamp = s/,"time":\d+//
https://regex101.com/r/Ecb0rZ/1
NOTE: SEDCMD takes place at indextime, but after timestamping happens, so if you use that timestamp to populate _time, that would still work.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you want to modify your raw events (and as a result also the fields that get extracted from those at searchtime), the SEDCMD in props.conf is usually the best option.
Can you share some sample raw events and an example of the desired output? Then we can sure help you with that.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
added the sample logs and requirement
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @rakeshksingh,
Go through this document to Discard specific events and keep the rest
http://docs.splunk.com/Documentation/Splunk/latest/Forwarding/Routeandfilterdatad#Filter_event_data_...
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It will be discarding specific events but not fields of that event.
sample logs :-
{"message":" 2017-06-12 08:32:30,585 INFO main org.apache.coyote.ajp.AjpNioProtocol - Initializing ProtocolHandler [\"ajp-nio-8009\"]","time":1497256350}
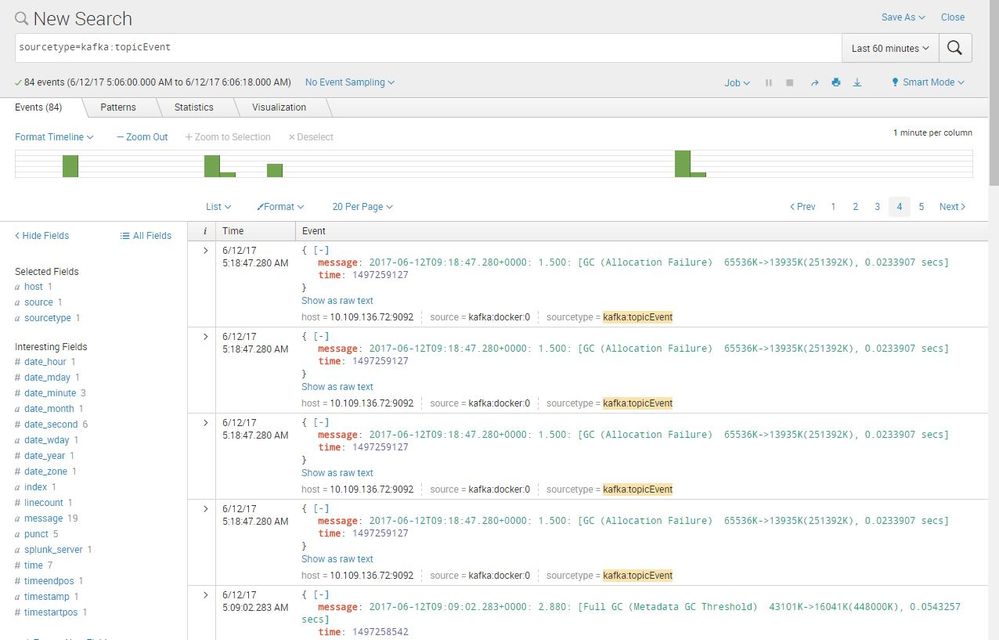
https://answers.splunk.com/storage/temp/205746-kafkadocker.jpg
So i need only message fields
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi @rakeshksingh
try like this ..
index=summary_data where field=4
Harish
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for query but it all the fields are in one raw event