Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How do I edit my timechart search to show all requ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OldManEd
Builder
08-11-2015
10:29 AM
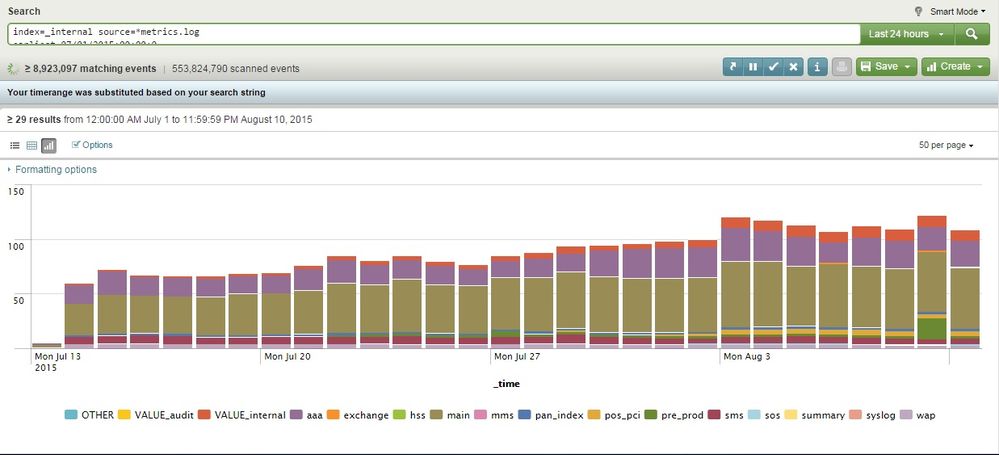
I am running the following search:
index=_internal source=*metrics.log
earliest=07/01/2015:00:00:0
latest=08/10/2015:23:59:59
| eval GB=kb/(1024*1024)
| search group="per_index_thruput"
| timechart span=1d sum(GB) by series limit=15
But when I run it, the chart data only goes back to July 13th.
Is there any way I can change the search to display all the data?
~Ed
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
somesoni2
Revered Legend
08-11-2015
11:06 AM
The default retention period of the _internal index is 30 days (in indexes.conf on Indexers, frozenTimePeriodInSecs = 2592000). That's why the data that you see is approximately 30 days old. (there is no data to show beyond that point)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
somesoni2
Revered Legend
08-11-2015
11:06 AM
The default retention period of the _internal index is 30 days (in indexes.conf on Indexers, frozenTimePeriodInSecs = 2592000). That's why the data that you see is approximately 30 days old. (there is no data to show beyond that point)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OldManEd
Builder
08-11-2015
11:24 AM
Oh heck. thanks for the info.
~Ed
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
[Puzzles] Solve, Learn, Repeat: Character substitutions with Regular Expressions
This challenge was first posted on Slack #puzzles channelFor BORE at .conf23, we had a puzzle question which ...
Splunk Community Badges!
Hey everyone! Ready to earn some serious bragging rights in the community? Along with our existing badges ...
[Puzzles] Solve, Learn, Repeat: Matching cron expressions
This puzzle (first published here) is based on matching timestamps to cron expressions.All the timestamps ...