Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Help with Rex Commands
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Help with Rex Commands
Hi All,
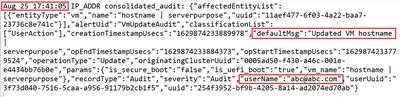
I am having some trouble extracing out the following with the following details
1. username
2. Default Msg
3. Date
4. Time
This is what I have tried and it gives me the username but I am stuck with how to extract the date , time and defaultmsg.
can someone please help me? Thank You so much
Index=xxx-xxx
| rex (?<username>\w+@\w+.\w+)
|table username DefaultMsg Date TIme
Thank You
regards,
Alex
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May I check if I can use eval command to actually filter to stop the data from showing up?
If yes, would anyone please show me how to use eval command?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Probably yes, but can you create a new question for that where you give example with data and result what you are meaning. For that way it's easier for community members found this question later on.
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why not use spath to extract data from the json part?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You're 100% right - spath does manipulation on a higher level so with bigger amounts of dataraw regex manipulation might indeed be faster. But spath is faster to write and might just be quick enough.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sure. First extract the raw json part into a field, then use spath to extract a value from json. Like that:
| rex "(?<jsondata>{.*})" | spath input=jsondata path="defaultMsg" | spath input=jsondata path="userName"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @splunknewbie81,
Please try this regex
| rex "(?ms)^(?<date>\w+\s\d+)\s+(?<Time>\d+:\d+:\d+).*defaultMsg\":\"(?<defaultMsg>[^\"]+).*userName\":\"(?<userName>[^\"]+)"that you can test at https://regex101.com/r/EGsp5X/1
If you could share the ssample logs in text format instead image, I could be more precise.
ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @splunknewbie81,
OK, I confirm the previous regex.
Ciao.
Giuseppe
P.S.: for the next time, put the logs in the Insert/edit code sample button (the one with </>), it's easier than a pdf.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
Index=xxx-xxx
| rex ^(?<Date>\w+\s\d+)\s(?<Time>\d+:\d+:\d+).+\"defaultMsg\":\s*\"(?<DefaultMsg>[^\"]+)\".+\"userName\":\s*\"(?<username>[^\"]+)\"
|table username DefaultMsg Date TIme- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
in next time we prefer those events as text, so it's easier to check and create that rex 😉
You could try this:
....
| rex "\"defaultMsg\":\"(?<defaultMsg>[^\"]+)\".*\"userName\":\"(?<userName>[^\"]+)"https://regex101.com/r/AtrUKE/1 You could test it with this.
Date and time you should get correctly on indexing time. Then you can take those from _time like
....
| eval date = strftime(_time, "%Y-%m-%d"), time = strftime(_time, "%H:%M:%S")
| eval dispDateTime = strftime(_time, "%b %d %H:%M:%s")r. Ismo