Join the Conversation
- Find Answers
- :
- Splunk Platform
- :
- Splunk Enterprise
- :
- Re: Why is DHCP log not parsing properly?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
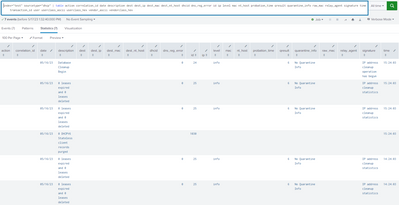
Hi, i have parsing issue on window DHCP log. Im using splunk add on for Window DHCP. The raw log are as below.
1030,05/16/23,15:24:03,0 DHCPV6 Stateless client records purged,,,,,,,,,,
25,05/16/23,15:24:03,0 leases expired and 0 leases deleted,,,,,0,6,,,,,,,,,0
25,05/16/23,15:24:03,0 leases expired and 0 leases deleted,,,,,0,6,,,,,,,,,0
24,05/16/23,15:24:03,Database Cleanup Begin,,,,,0,6,,,,,,,,,0
11030,05/16/23,14:24:03,0 DHCPV6 Stateless client records purged,,,,,,,,,,
25,05/16/23,14:24:03,0 leases expired and 0 leases deleted,,,,,0,6,,,,,,,,,0
25,05/16/23,14:24:03,0 leases expired and 0 leases deleted,,,,,0,6,,,,,,,,,0
it seems like doesn't have any information.
Please assist for this issue.
Thank You
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I installed that app and loaded your data. It appears to parse just fine.
As far as I can tell, the empty fields are empty because they're not in the sample events.
The TA expects these fields in this order.
"id","date","time","description","ip","nt_host","mac","user","transaction_id","qresult","probation_time","correlation_id","dhcid","vendorclass_hex","vendor_ascii","userclass_hex","userclass_ascii","relay_agent","dns_reg_error"If you're getting results like these then perhaps consider re-installing the TA.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Which app are you using (please share the splunkbase URL)? Is it installed on your indexers and heavy forwarders? Did you restart them after installation?
It seems like the data doesn't match the props supplied by the app. You may need to modify settings to match your data. Knowing the exact app will help us be more specific.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
the app URL is as below:
Microsoft Windows DHCP addon for Splunk | Splunkbase
the app installed in search head and indexers, the data source is from UF. Already restart after the app installation.
Please advise, thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I installed that app and loaded your data. It appears to parse just fine.
As far as I can tell, the empty fields are empty because they're not in the sample events.
The TA expects these fields in this order.
"id","date","time","description","ip","nt_host","mac","user","transaction_id","qresult","probation_time","correlation_id","dhcid","vendorclass_hex","vendor_ascii","userclass_hex","userclass_ascii","relay_agent","dns_reg_error"If you're getting results like these then perhaps consider re-installing the TA.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi richgalloway,
Thank you for the reply. The actual event should be containing user's information but in splunk raw event we didn't receive much information.
i think we need to check the log from the DCHP server itself.
Thank you for your assist.