Are you a member of the Splunk Community?
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- Re: CIM help
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
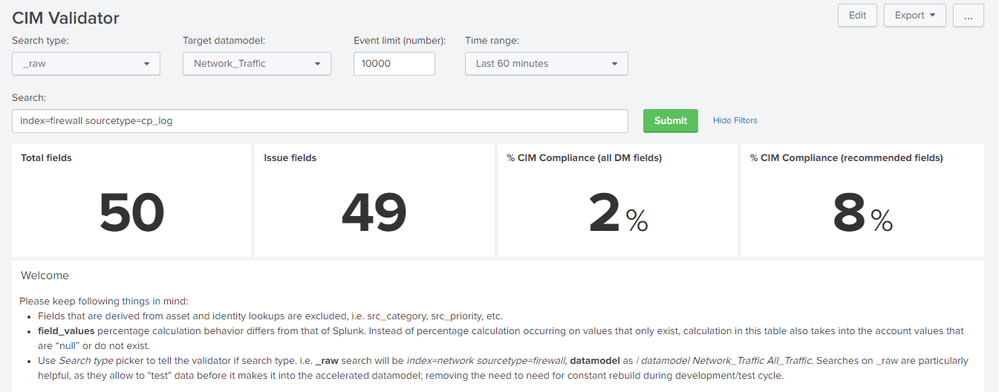
I'm reviewing the logs to make sure the fields match the Splunk Enterprise Security CIM and datamodels.
The query shows me this percentage, understanding that they are the fields that are required versus the fields that it is finding, in this order of ideas, to adjust these fields I must create an alias or I must perform an "extract" either by regular expressions or tabs?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
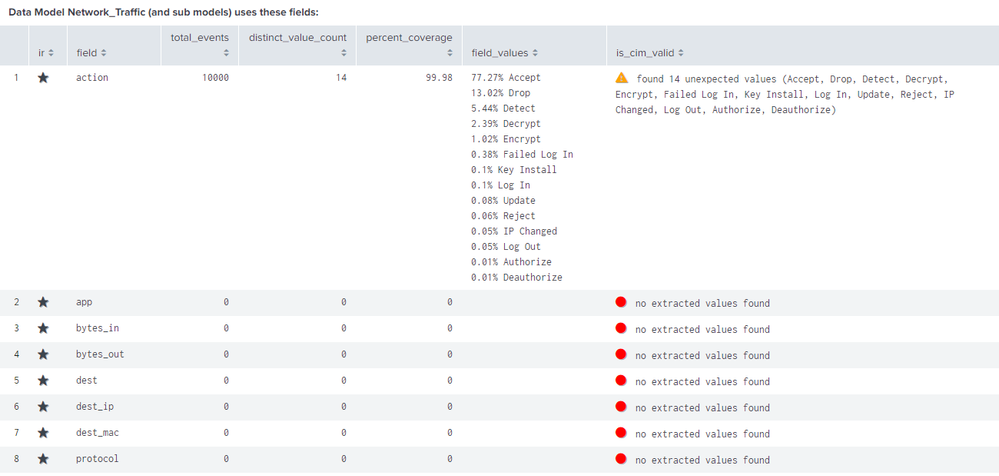
Per documentation, for example the action field in network traffic datamodel, prescribed values are allowed, blocked and teardown. But you have many values under action field. As suggested above, you can create a calculated field like
| eval action=case((action="xxx" OR action="yyy"),"allowed",1=1,"blocked")
Doing this on all recommended fields will increase you compliance %
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Per documentation, for example the action field in network traffic datamodel, prescribed values are allowed, blocked and teardown. But you have many values under action field. As suggested above, you can create a calculated field like
| eval action=case((action="xxx" OR action="yyy"),"allowed",1=1,"blocked")
Doing this on all recommended fields will increase you compliance %
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, you need to extract fields or create aliases to increase your CIM compliance.
If this reply helps you, Karma would be appreciated.