Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Enterprise Security
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- Active Directory - Event ID 4738 - Message Fields
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Active Directory - Event ID 4738 - Message Fields
fzuazo
Path Finder
08-28-2018
11:59 AM
I seem to be having some issues working with AD event ID 4738. Unless I am doing or reading something wrong, one of the attributes clearly has a value in raw AD log yet Splunk does not seem to capture that value.
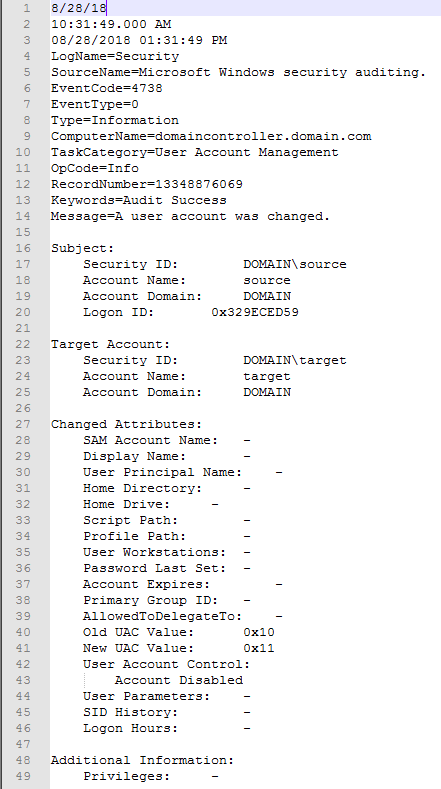
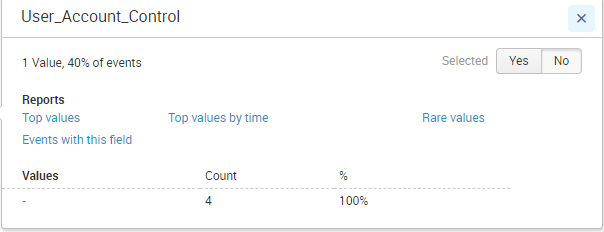
Below is a screenshot of an event 4738. See the "User Account Control" field and how it shows "Account Disabled". Under this screenshot I have included another showing how Splunk displays the returned values for that attribute. I have attempted to use REX but seeing as Splunk doesn't see the value for "User Account Control" it isn't returning anything.
My goal is to be able to create a table showing the source, target, the change, and time. I can populate the other columns just fine.
Any help is GREATLY appreciated.
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Splunk Lantern’s Guide to The Most Popular .conf25 Sessions
Splunk Lantern is a Splunk customer success center that provides advice from Splunk experts on valuable data ...
Unlock What’s Next: The Splunk Cloud Platform at .conf25
In just a few days, Boston will be buzzing as the Splunk team and thousands of community members come together ...
Index This | How many sevens are there between 1 and 100?
August 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...