Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Admin Other
- :
- Security
- :
- Regarding Log4j
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Regarding Log4j
Hello everyone,
So according to the Splunk blog: Splunk Security Advisory for Apache Log4j (CVE-2021-44228 and CVE-2021-45046) | Splunk it says that the affected versions are: "All supported non-Windows versions of 8.1.x and 8.2.x only if DFS is used. "
I'm using Splunk Enterprise Search Head & Indexer with version 7.3.1 and I can see various log4j-1.2.17.jar files under location "/bin/jars/vendors/spark/2.3.0/lib/", "/etc/apps/splunk_app_db_connect/bin/lib/", /etc/apps/splunk_archiver/java-bin/jars/vendors/spark/ and etc.
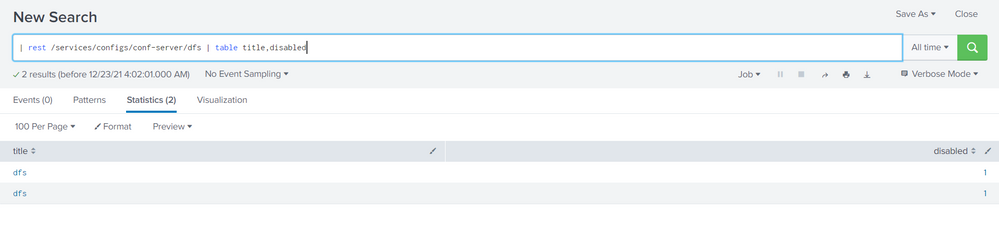
Also, I am attaching the result I received from a search query to determine if DFS is enabled on my Splunk servers.
Should I be concerned about this vulnerability?
Also to remediate, do I just need to replace this log4j-1.2.17.jar with the latest files directly in the respective directories or do I need to make any changes in the conf files as well?
Any help will be appreciated.
Thank you!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Since you're running an unsupported version of Splunk, the guidance in the blog doesn't apply. We can make some reasonable conclusions from it, however.
You're not using DFS so you should be safe.
To be "safer", follow the remediation instructions and remove the vulnerable jar files.
The instructions say nothing about changing config files so no changes are necessary.
To be "safest", upgrade to a version of Splunk that fixes the vulnerability.
If this reply helps you, Karma would be appreciated.