- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: LINE_BREAKER settings works when adding input ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
LINE_BREAKER settings works when adding input manually but not through props.conf
Hi,
I am trying to add Snort data into Splunk by monitoring barnyard2.alert file using Universal Forwarders.
[monitor:///var/log/barnyard2/barnyard2.alert]
sourcetype=snort_unified2
index=snort
As explained here https://community.splunk.com/t5/Getting-Data-In/Why-is-Splunk-line-breaking-a-single-IDS-Alert-event... , I added same settings to props.conf(Indexer and SH) but Splunk still ends up breaking each line as a separate event, as shown below:
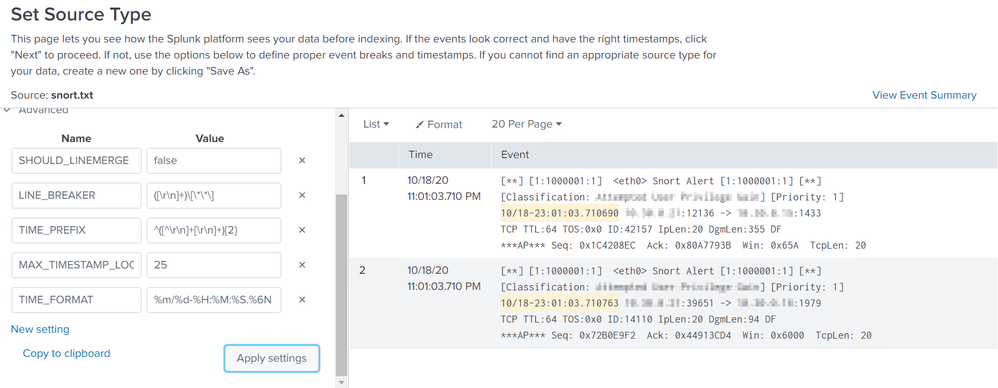
props.conf
[snort_unified2]
SHOULD_LINEMERGE = false
LINE_BREAKER = ([\r\n]+)\[\*\*\]
TIME_PREFIX = ^([^\r\n]+[\r\n]+){2}
MAX_TIMESTAMP_LOOKAHEAD = 25
TIME_FORMAT = %m/%d-%H:%M:%S.%6N
category = Network & Security
But when I try these settings by manually adding same input it works just fine.
Any ideas on what could be going wrong with props.conf?
Thanks,
~Abhi
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is an index time setting and therefore not required at universal forwarder.
Here is what you can try:
SHOULD_LINEMERGE= true
Along with one of:
BREAK_ONLY_BEFORE,
BREAK_ONLY_AFTER
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @att35 ,
check props.conf on your UF or try using btool command.
Please let me know if it helps or you found solution already.
Thanks
Sam
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @samcyber20
App that we pushed on the endpoints to collect these logs does not have any props.conf. Only inputs.conf with one stanza as I mentioned above.
Does it need a props as well with any of the entries that I added on the Indexer side?
Thanks,
~ Abhi
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
splunk btool props list -debug snort_unified2
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you restart the indexers after changing the props.conf file?
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @richgalloway ,
Yes. Both Indexer and the Search Head were restarted after making the props.conf change.
Thanks,
~ Abhi