Are you a member of the Splunk Community?
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: How to monitor [WinEventLog://System] event l...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
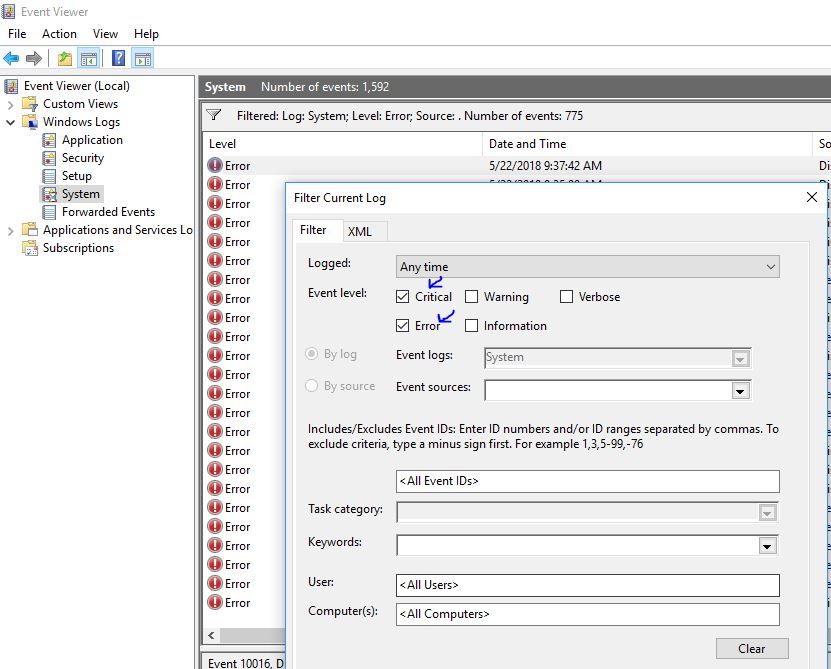
How to monitor [WinEventLog://System] event logs for "Critical" or "Error" event logs only (Level 1 and 2)
Is there any way to monitor System Event Viewer logs ( [WinEventLog://System] ) for Event Level set to "Critical" and/or "Error" only (Level =1 or 2) ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It appears Splunk should allow you to whitelist based on Type, which is the field/key where the level is sent.
I would start with:
whitelist = Type="^[1|2]"
references:
http://docs.splunk.com/Documentation/Splunk/7.1.1/Data/MonitorWindowseventlogdata#Create_advanced_fi...
https://msdn.microsoft.com/en-us/library/aa394226(v=vs.85).aspx
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@danielransell , confirmed. I was able to test it yesterday: used "whitelist = Type = "Error" " in our test environment
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think you want to look at whitelisting for this. I have blacklisted certain event codes when ingesting security logs - I believe you can also perform whitelisting, that is on ingest events that meet a particular criteria.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@danielransell we whitelist Event Codes , for example. But cannot find any mentioning on how to whitelist Levels (Critical, Error)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To whitelist levels, you would need to create a whitelist regex. you should be able to mix event IDs and regex with separate lines like so:
whitelist1 = <list of eventIDs>
whitelist2 = key=regex [key=regex]
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@ jconger , it's not clear to me what you mean. can you , please, give more details or examples?
We are trying to get errors no matter what event ID is.