Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: Error while adding more than 1 Cisco device
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Error while adding more than 1 Cisco device
Dear Experts,
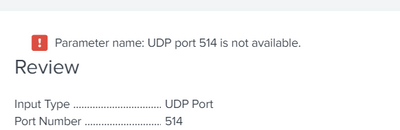
I am trying to add the data to monitor Cisco logs through Splunk, i am just able to add 1 device only, it is giving error when i am adding more devices.
Snapshot of the error is shown below.
Any help regarding this will be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Will be thankful if there is any help regarding this
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello there. Consider using Splunk Connect for Syslog. It is a tool that will allow very easy implementation of datasources like Cisco through syslog-ng. It will ultimately write to HTTP Event Collector in Splunk.
See this link for additional information. I hope this helps because I have been having great success with this tool!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, have to check it.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It would help if you explained the steps to reproduce this problem, but I suspect you are doing at least two things wrong:
1) Trying to send syslog events directly to Splunk. This has been discouraged for a few years because it can lead to data loss. Best Practice is to send syslog events to a dedicated syslog server and forward them from there to Splunk.
2) Assuming there is a one-to-one relationship between a UDP port and a network device. This is not the case. Once Splunk is listening to a port, it will accept data from thousands of devices, provided they match the "Only accept connection from" setting.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It can be reproduce by doing the following,
Add Data > Monitor > TCP/UDP > then mention the port udp/514 and add any IP address in Only accept connection from field.
It is just accepting one device, and when i am trying to add another device, it is showing an error, as was mentioned in the snap in my last post.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you read point #2 in my answer? It doesn't make sense to add the same port multiple times. Once Splunk is listening to a port there is no need to tell it to do so again.
Please describe the problem you are trying to solve. What is it that adding another port 514 input will do for you?
If this reply helps you, Karma would be appreciated.