Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- XML Event Viewer Data Missing Message\Fields
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi All,
I was hoping that modification of KV_Mode=xml in props.conf under the [xmlwineventlog] stanza on the standalone index\search head\deployment server would properly parse the Event View data from servers, but unfortunately I am not seeing all the message data that should be included.
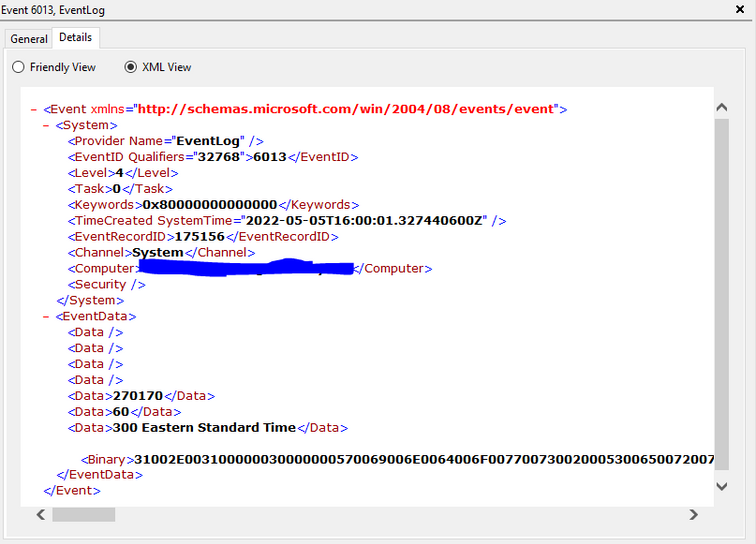
Here is sample of data, please see Event.EventData.Binary field:
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@VTARNG_Paul - That's the problem with Windows I always face is that XML data (which is a new version) is not always a replica of PlainText (Legacy) format.
My views:
- Collect PlainText - WinEventLog:Security, WinEventLog:System, etc
- Collect XML - Windows Defender Logs, etc
These are just some examples and my personal views on which has richer field information.
You need to look at the EventViewer and decide which one has the right fields that you need.
I hope this helps!!! Consider upvoting/accepting answer if this helped!!!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@VTARNG_Paul - Please look at the same event in Windows Event Viewer on the machine and see how you are seeing the fields and data.
Ideally, Splunk collects what is generated on the system.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
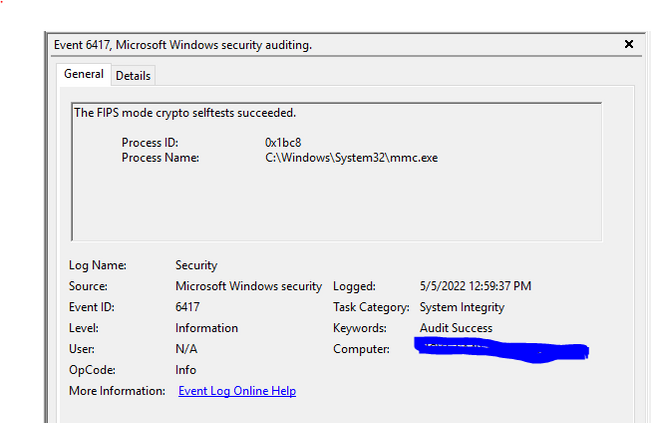
From sourcetype XmlWinEventLog we are missing the data in these Event Viewer fields located in the General tab in this screenshot. For example TaskCategory and Keywords.
It should be included as we are pulling the identical data from another server with sourcetype WinEventLog and all of those fields are in the events.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@VTARNG_Paul - Your Event Viewer should also show other sections as well for XML.
This screenshot is what PlainText formatted is what you can get in Splunk if you enable PlainText format event with inputs.conf.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
You are correct the Message field is not included and other fields that I would like to use have generic names, Data, which is not very helpful for the reports/dashboard I want to make.
We are using xml because it requires less storage space and possibly faster, but have not really seen any performance advantage from my testing so far.
I think we might have to rethink the xml version of that data.
Cheers, Paul
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@VTARNG_Paul - That's the problem with Windows I always face is that XML data (which is a new version) is not always a replica of PlainText (Legacy) format.
My views:
- Collect PlainText - WinEventLog:Security, WinEventLog:System, etc
- Collect XML - Windows Defender Logs, etc
These are just some examples and my personal views on which has richer field information.
You need to look at the EventViewer and decide which one has the right fields that you need.
I hope this helps!!! Consider upvoting/accepting answer if this helped!!!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The KV_Mode=xml setting will have no effect on that data since it is not in XML format.
Check the source application to see if there is a setting that will change the format to something non-binary.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I am not seeing any non-binary setting for Event Viewer data.
Thanks!