Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Dashboards & Visualizations
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Dashboard - Base search results differs from no sa...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
afsku
Engager
03-22-2021
12:52 PM
Hi,
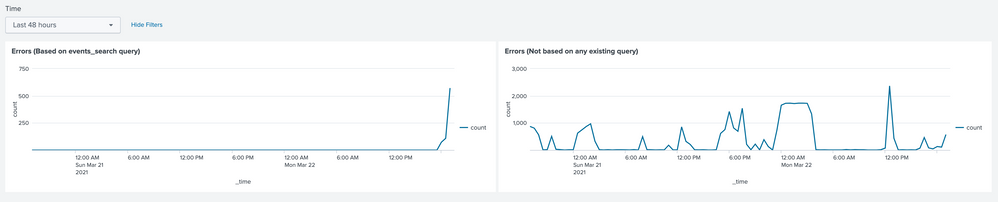
I have two identical queries on the dashboard, the only difference - one is based on previously defined search results. They produce very different charts however, here is the code and screenshots:
<form>
<search id="events_search">
<query>
index = "*" | fields *
</query>
<earliest>$time_token.earliest$</earliest>
<latest>$time_token.latest$</latest>
</search>
<fieldset submitButton="false" autoRun="true">
<input type="time" token="time_token">
<label>Time</label>
<default>
<earliest>-48h@h</earliest>
<latest>now</latest>
</default>
</input>
</fieldset>
<row>
<panel>
<chart>
<title>Errors (Based on events_search query)</title>
<search base="events_search">
<query> search level IN ("error", "fatal") | timechart count
</query>
</search>
<option name="charting.chart">line</option>
<option name="charting.drilldown">all</option>
<option name="refresh.display">progressbar</option>
</chart>
</panel>
<panel>
<chart>
<title>Errors (Not based on any existing query)</title>
<search>
<query> index = "*" | fields * | search level IN ("error", "fatal") | timechart count
</query>
<earliest>-48h@h</earliest>
<latest>now</latest>
</search>
<option name="charting.chart">line</option>
<option name="charting.drilldown">all</option>
<option name="refresh.display">progressbar</option>
</chart>
</panel>
</row>
</form>
So I wonder if it is a bug or some sort of known behavior?
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
03-22-2021
02:19 PM
Hi
This is known limitation of using none transforming base search. It return only xx k (500k if I recall right) results.
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
03-22-2021
02:19 PM
Hi
This is known limitation of using none transforming base search. It return only xx k (500k if I recall right) results.
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
afsku
Engager
03-22-2021
04:00 PM
Thanks, @isoutamo , I should have read Optimizing Splunk Dashboards with Post-Process Searches , now I got my searches optimized and problem has gone.
Get Updates on the Splunk Community!
Index This | Why did the turkey cross the road?
November 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...
Enter the Agentic Era with Splunk AI Assistant for SPL 1.4
🚀 Your data just got a serious AI upgrade — are you ready?
Say hello to the Agentic Era with the ...
Feel the Splunk Love: Real Stories from Real Customers
Hello Splunk Community,
What’s the best part of hearing how our customers use Splunk? Easy: the positive ...