- Splunk Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Create TimeSpan Line Chart After Eval-ing
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
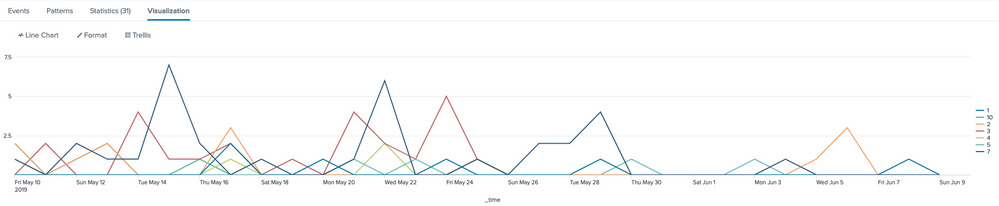
Do any experienced Splunkers know what needs to be changed to my query below in order to create a TimeSpan Line Chart over say the past 30 days for counts of the four Severity levels created by the Eval command?
index=myIndex source=mySource host=myHost sourcetype=mySourceType | stats count(eval(severity="0" OR severity="1" OR severity="2")) as Low count(eval(severity="3" OR severity="4" OR severity="5")) as Medium count(eval(severity="6" OR severity="7" OR severity="8")) as High count(eval(severity="9" OR severity="10")) as Critical | table Low Medium High Critical | transpose | rename column as Severity "row 1" as Count
I have attached a screenshot and instead of the values on the right-hand side being 1 - 10, I'd like them to be Low, Medium etc...
Thanks in advance
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this untested query:
index=myIndex source=mySource host=myHost sourcetype=mySourceType
| eval Severity=case(severity="0" OR severity="1" OR severity="2"), "Low", (severity="3" OR severity="4" OR severity="5"), "Medium", (severity="6" OR severity="7" OR severity="8"), "High", (severity="9" OR severity="10"), "Critical")
| timechart count as Count by Severity
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this untested query:
index=myIndex source=mySource host=myHost sourcetype=mySourceType
| eval Severity=case(severity="0" OR severity="1" OR severity="2"), "Low", (severity="3" OR severity="4" OR severity="5"), "Medium", (severity="6" OR severity="7" OR severity="8"), "High", (severity="9" OR severity="10"), "Critical")
| timechart count as Count by Severity
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the input. It didn't work when I tried it but I took your command, switched it up a little and positioned it further up the query and it worked:
index=myIndex source=mySource host=myHost sourcetype=mySourceType | timechart count(eval(severity="0" OR severity="1" OR severity="2")) as Low count(eval(severity="3" OR severity="4" OR severity="5")) as Medium count(eval(severity="6" OR severity="7" OR severity="8")) as High count(eval(severity="9" OR severity="10")) as Critical
Again, thanks for your help on this!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@migquinn If your problem is resolved, please accept the answer to help future readers.
If this reply helps you, Karma would be appreciated.