Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Sourcetype WinEventLog:Security
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi team
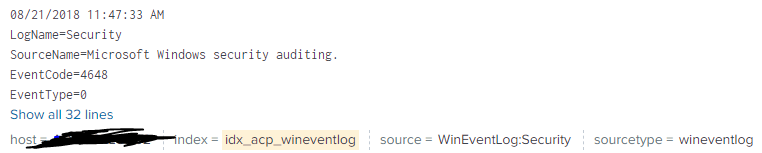
i always work with the Add-On "splunk for windows" for monitoring security events, it always brings me the data with "sourceytpe=WinEventLog:Security", but i don't know if the last version changes the sourcetye by wineventlog, i attached a picture with example, i need to have the "Sourcetype=WinEventLog:Security" with my data
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure which version TA you're using. I found below in props.conf in default directory of Splunk_TA_windows version 5.0.0. More about renaming sourcetypes.
## To provide backward compatibility for WinEventLog and XmlWinEventLog data
## These will be deprecated in future
[WinEventLog:Security]
rename = wineventlog
If your props.conf have the above attribute, then comment rename command (and restart splunk) OR try renaming wineventlog to WinEventLog:Security in props.conf under local directory to see if this solves your problem.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure which version TA you're using. I found below in props.conf in default directory of Splunk_TA_windows version 5.0.0. More about renaming sourcetypes.
## To provide backward compatibility for WinEventLog and XmlWinEventLog data
## These will be deprecated in future
[WinEventLog:Security]
rename = wineventlog
If your props.conf have the above attribute, then comment rename command (and restart splunk) OR try renaming wineventlog to WinEventLog:Security in props.conf under local directory to see if this solves your problem.