Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- Only one alert needs to be triggered in the Alert ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Only one alert needs to be triggered in the Alert Manager?
Hello Splunkers,
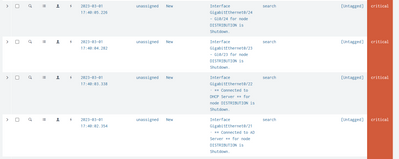
I have switches from which the logs are getting ingested into splunk. So when the specific multiple interfaces are down it should trigger me only one alert. At present i am using the below query
index="switches"| spath Message
|search Message="*Interface GigabitEthernet0/21 · ** Connected to AD Server ** for node DISTRIBUTION is Shutdown."
OR Message="Interface GigabitEthernet0/23 - Gi0/23 for node DISTRIBUTION is Shutdown."
OR Message="Interface GigabitEthernet0/24 - Gi0/24 for node DISTRIBUTION is Shutdown."
OR Message="*Interface GigabitEthernet0/22 · ** Connected to DHCP Server ** for node DISTRIBUTION is Shutdown."
|table _time Message Device_Name
Here when any one interface is down or multiple interface is down then the number of alert is getting triggered depending on the number of interfaces down. Now what i need is that if there are multiple interfaces down, it should raise only one alert in alert manager. I have attached the screenshot of the alerts when the multiple interfaces are down.
Thanks in Advance..
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
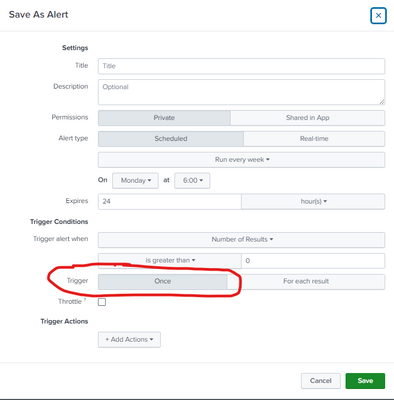
It sounds like the alert is configured to trigger for each result instead of once per run.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @richgalloway
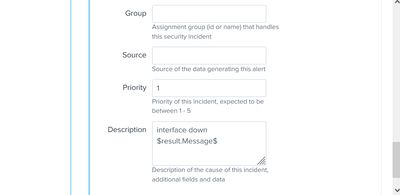
Thank you for the response and it helped me and i am seeing only one alert in alertmanager with the fields and i want to let you know that i have integrated ServiceNow with splunk also, so when this alert is getting triggered its raising an incident in the ServiceNow and in the incident description its only giving the first log message only, so is there any way to get all the logs messages into the ticket description.
(In short: When the 4 interfaces are down the incident is created in servicenow with only first log mesage field. so is there any way to get all the message fields that are available in the alert in ServiceNow Incident)
The alert is configured in ServiceNow app as below mentioned Screenshot:
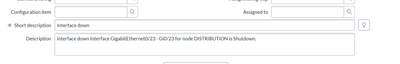
The incident raised in the ServiceNow screenshot:
Thanks in advance....
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The construct $result.foo$ always returns the first instance of the foo field. Splunk does not provide a way to get all results, except via a link (which probably won't work with SNOW).
You may have to go back to having separate alerts for each device.
If this reply helps you, Karma would be appreciated.