Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- Re: How to set alert to know any alert Script is r...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to set alert to know any alert Script is ran/not for the scheduled alert
Hello!
Can anyone please help how to know if we ran an alert/not for a scheduled alert?
We set the below alert for every Monday 6:00 am.
Alert Example:
| makeresults
| eval ip_ports = "10.120.121.100:9443"
| eval ip_ports = split(ip_ports,",")
| mvexpand ip_ports
| rex field=ip_ports "(?<dest>[^:]+):(?<dest_port>\d+)"
| table dest dest_port
| lookup sslcert_lookup dest dest_port
| eval days_left = round(ssl_validity_window/86400)
| eval ssl_end_time=strftime(ssl_end_time,"%Y-%m-%d")
| eval ssl_start_time=strftime(ssl_start_time,"%Y-%m-%d")
| where days_left < 60
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk logs that for you. Search the logs with a query like this:
index=_internal source=*scheduler.log search_type=scheduled savedsearch_name="<alert name>"
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@richgalloway Hello, thanks for the query i got great results, so some more need to do based on the below query, I need an alert for if any of the searches are not run I need the alert to mail.
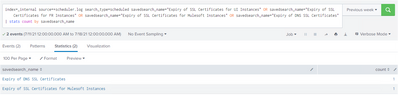
index=_internal source=*scheduler.log search_type=scheduled savedsearch_name="Expiry of SSL Certificates for UI Instances" OR savedsearch_name="Expiry of SSL Certificates for FR Instances" OR savedsearch_name="Expiry of SSL Certificates for Mulesoft Instances" OR savedsearch_name="Expiry of DNS SSL Certificates"
| stats count by savedsearch_name
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Search for status != success
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@richgalloway I didn`t get any results other than success. I need other than success saved alerts out of 4.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Congratulations! None of your alerts failed to run. Save that search as an alert and have it trigger when the number of results is not zero. That will happen when status!=success some time in the future.
If this reply helps you, Karma would be appreciated.