Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: using eval to calculate time between events no...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am trying to use eval to calculate the time between events. Those events have a unique ID.
This is the sarch that I have now:
<my search>
| eval Test =if(message.information=="some_data",_time,null())
| eval Test2=if(message.information="some_data_2" ,_time,null())
| eval Test3 = Test - Test2
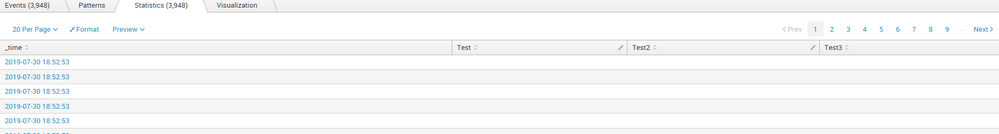
| table _time Test Test2 Test3
I am doing something wrong I guess because I only see values in the _time column, the rest is empty.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Mike6960,
you need to put your message.information fields in single quotes ' like this:
<my search>
| eval Test =if('message.information'=="some_data",_time,null())
| eval Test2=if('message.information'="some_data_2" ,_time,null())
| eval Test3 = Test - Test2
| table _time Test Test2 Test3
because they contain a . and this is a special case when using eval()
Take a look at this run everywhere SPL:
| makeresults
| eval message.information="1", foo="2"
| eval Test =if('message.information'=="1",now(),null())
| eval Test2=if('message.information'=="2" ,null(),relative_time(now(), "-1sec"))
| eval Test3 = Test - Test2
| table _time Test Test2 Test3
Hope this helps ...
cheers, MuS
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Mike6960,
you need to put your message.information fields in single quotes ' like this:
<my search>
| eval Test =if('message.information'=="some_data",_time,null())
| eval Test2=if('message.information'="some_data_2" ,_time,null())
| eval Test3 = Test - Test2
| table _time Test Test2 Test3
because they contain a . and this is a special case when using eval()
Take a look at this run everywhere SPL:
| makeresults
| eval message.information="1", foo="2"
| eval Test =if('message.information'=="1",now(),null())
| eval Test2=if('message.information'=="2" ,null(),relative_time(now(), "-1sec"))
| eval Test3 = Test - Test2
| table _time Test Test2 Test3
Hope this helps ...
cheers, MuS
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MuS Thanks, this works. I now only have to convert to normal time, because I get a number as result. Is there a way to show one line per ID? What I mean is that in the example I gave there are always tow events per ID. Ik want one line per ID.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry, but there is no id in this question and I also don't know what your events look like or your expected output looks like. This is really up to you to figure it out or accept this answer and post a new one with more details.
cheers, MuS
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok, thank you for your help with my initial question
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You're welcome 🙂
cheers, MuS
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MuS , also the field Test3 remains empty...