Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- sum multiple fields based on the field only
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Splunkers
in my firewall logs, i have three numerical fields, (out_packet, in_packet, bytes)
i want to sum these values each field individually but a i want the answer in one record
for example:
index=firewall
| timechart sum (bytes) as bytes , sum (in_packet) as in_packet, sum (out_packet) as out_packet
unfortunately it didn't work, please help me with it
Thanks ^_^
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
index=firewall
| stats sum (bytes) as bytes , sum (in_packet) as in_packet, sum (out_packet) as out_packet- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
index=firewall
| stats sum (bytes) as bytes , sum (in_packet) as in_packet, sum (out_packet) as out_packet- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the prompt response ^_^
but i need it in time chart for visualization, help me with it plz
Thanks ^_ ^
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Stats will give you one record as you said. Timechart will give you lots of records (assuming the time span is wide enough). How are the results you originally had not what you wanted?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry, i just noticed that my post was confusing
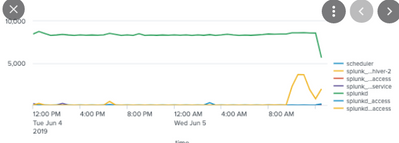
what i want is to show the the trends of these three fields in a "line chart" visualization
i want the trend by any value of my choosing
for example i want like this, but with multiple fields based on the search
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is still not clear why timechart is not working for you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
wait, the problem if from my side, my log sources have missing data.
sorry for that, BTW you helped my a lot in many posts, thanks whisperer ^_^