Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Why does appendcols only show a fraction of overal...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why does appendcols only show a fraction of overall search?
sbentley_ea
Explorer
11-14-2019
09:53 AM
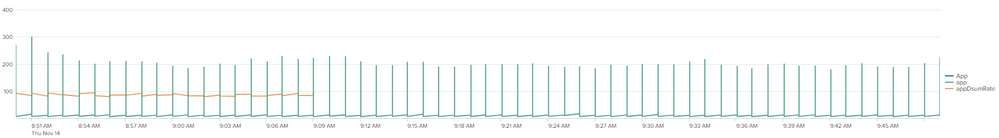
index=* App=appA OR appB OR appC |
stats sum(Rate) as appSumRate by _time, App |
appendcols [ search index=* App=appD |
stats sum(Rate) as appDsumRate by _time, App ]
When I try the above search I only get a fraction of the subsearch results, no matter what timerange.
When I do the appendcols subsearch by itself, it gets the full timerange.
What can I do to increase the range?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
woodcock
Esteemed Legend
11-14-2019
04:39 PM
It is best not to use it. Try this:
(index=* App IN("appA", "appB", "appC", "apD")
| eval AppCategory=if(App=="appD", "appD", "appsABC")
| timechart sum(Rate) AS appSumRate BY AppCategory
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sbentley_ea
Explorer
11-18-2019
10:20 AM
I wanted to separate the appSumRate by Apps and when I use this I only get two categories. To add on to what I was trying to do, with appDsumRate, I wanted to use it to get the ratios relative to the rest of the apps.
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Take Action Automatically on Splunk Alerts with Red Hat Ansible Automation Platform
Are you ready to revolutionize your IT operations? As digital transformation accelerates, the demand for ...
Calling All Security Pros: Ready to Race Through Boston?
Hey Splunkers,
.conf25 is heading to Boston and we’re kicking things off with something bold, competitive, and ...
Beyond Detection: How Splunk and Cisco Integrated Security Platforms Transform ...
Financial services organizations face an impossible equation: maintain 99.9% uptime for mission-critical ...