Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Why are there issues with delta query by multiple ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why are there issues with delta query by multiple hostnames?
thaghost99
Path Finder
03-09-2022
10:26 AM
index=testlab sourcetype=testcsv
| rex field="status detail" "(?<message_received_name>Messages Received)\\s*[0-9,]*\s*[0-9,]*\s*(?<message_received>[0-9,]*)"
| rex field=message_received mode=sed "s/,//g"
| eval myInt = tonumber(message_received)
| reverse
| delta myInt as message_received_delta
| timechart span=10m sum(message_received_delta) by Hostname
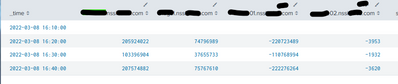
the problem i find is that when i am doing only 1 hostname at a time. it works just fine. (note the data is incremental counters only). but when i introduce additional hostnames, i see some hostnames would show a negative value. it should only show positive numbers (0 to inifinity)
again when i do single host, it works just fine. 🙂 really need help on this one.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
bowesmana

SplunkTrust
03-09-2022
02:20 PM
Unfortunately delta works simply on the message stream and does not support any 'by FIELD' construct.
You need to use streamstats for that - note that when splitting by fields in streamstats you need to use the global=f flag.
Take a look at the reply to your other message which shows you the streamstats construct that should work.
Kudos for experimenting! Good to learn.
Get Updates on the Splunk Community!
Splunk Mobile: Your Brand-New Home Screen
Meet Your New Mobile Hub
Hello Splunk Community!
Staying connected to your data—no matter where you are—is ...
Introducing Value Insights (Beta): Understand the Business Impact your organization ...
Real progress on your strategic priorities starts with knowing the business outcomes your teams are delivering ...
Enterprise Security (ES) Essentials 8.3 is Now GA — Smarter Detections, Faster ...
As of today, Enterprise Security (ES) Essentials 8.3 is now generally available, helping SOC teams simplify ...