Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Concact msg from multiple event for after appl...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello All , thanks for the help, my exemple:
| logStreamName: | _time | message |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout |
9/20/2211:22:23.295 AM |
allo |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout | 9/20/2211:22:23.295 AM | allo1 |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout | 9/20/2211:23:23.295 AM | Erreur |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout | 9/20/2211:23:24.195 AM | allo2 |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout |
9/20/2211:23:24.195 AM |
allo4 |
I want get this output, for apply after regex for extract some line around the erreur msg
| logStreamName: | _time | ms |
| 09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout | 9/20/2211:22:23.295 AM |
allo allo1 Error allo2 allo4 |
if i try that search
index="bnc_6261_pr_log_conf" logStreamName="*/i-09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout" | stats count by logStreamName | map maxsearches=20 search=" search index="bnc_6261_pr_log_conf" logStreamName=$logStreamName$ | eval ms=_time + message| stats values(ms) by logStreamName,_time "| transaction logStreamName | rex field=ms "(?<ERROR_MESSAGE>.{0,50}Error.{0,50})" it is not working if I perform the rex on msg, if I try use rex on logStreamName with different search string it is work, i try use transaction command for concact msg.
and I create ms variable for add time to my msg , it force too keep the order of message, it the only whey a found.
Please help me.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello , I find a solytion base on what you give me.
index="bnc_6261_pr_log_conf" logStreamName="*/i-09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout" | eval ms=_time + message| stats list(ms) as msg by logStreamName | rex field=msg "(?<Err_Mss>.((.*\n){0,3}).*disk\ space*((.*\n){0,3}))"
Thanks fo your help
Hugues
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does this work for you?
| stats list(message) as ms by logStreamName _time- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello , I find a solytion base on what you give me.
index="bnc_6261_pr_log_conf" logStreamName="*/i-09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout" | eval ms=_time + message| stats list(ms) as msg by logStreamName | rex field=msg "(?<Err_Mss>.((.*\n){0,3}).*disk\ space*((.*\n){0,3}))"
Thanks fo your help
Hugues
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
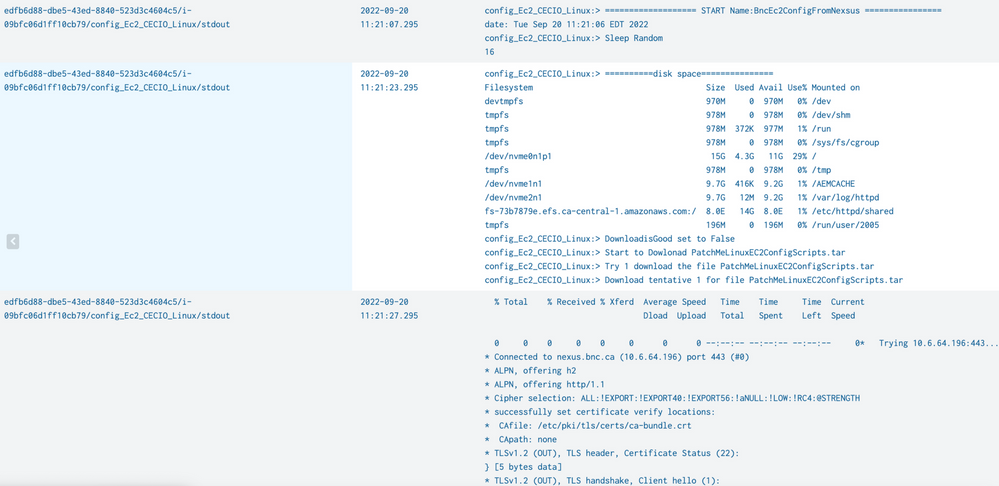
Thanks for your try, is not working , see the output
my search base on what you give me
index="bnc_6261_pr_log_conf" logStreamName="*/i-09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout" | stats count by logStreamName | map maxsearches=20 search=" search index="bnc_6261_pr_log_conf" logStreamName=$logStreamName$ | stats list(message) as ms by logStreamName _time"
and i try too
index="bnc_6261_pr_log_conf" logStreamName="*/i-09bfc06d1ff10cb79/config_Ec2_CECIO_Linux/stdout" | stats list(message) as ms by logStreamName _time