Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Using stats dc with stats list and count
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jwalzerpitt
Influencer
01-16-2019
11:23 AM
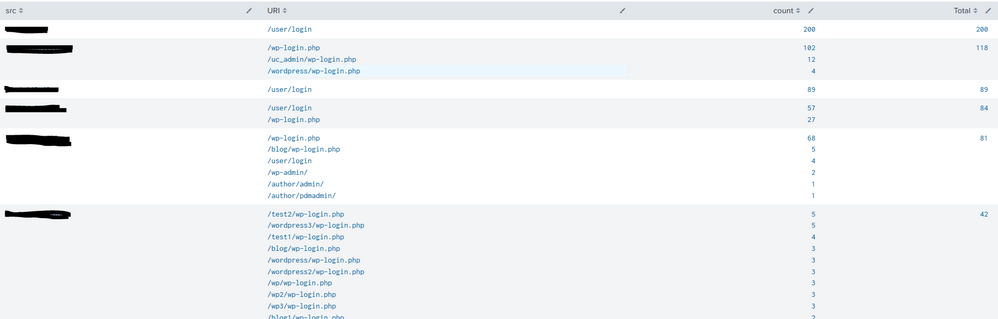
I have the following search looking for external hosts that are trying to brute force multiple WordPress or Drupal sites:
index=foo sourcetype="f5:bigip:asm:syslog" action!=blocked uri="/*login.php" OR uri="/*admin/" OR uri="*user\/login" uri!="*revslider*" action!=blocked
| stats count by src uri
| sort -count
| stats list(uri) as URI, list(count) as count, sum(count) as Total by src
| sort -Total
| head 10
Output is as follows:
How can I utilize stats dc to return only those results that have >5 URIs?
Thx
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vnravikumar
Champion
01-16-2019
12:18 PM
Hi @jwalzerpitt
Please try
| stats dc(uri) as distinct_uri, values(uri) as URI, values(count) as count, sum(count) as Total by src | where distinct_uri > 5
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vnravikumar
Champion
01-16-2019
12:18 PM
Hi @jwalzerpitt
Please try
| stats dc(uri) as distinct_uri, values(uri) as URI, values(count) as count, sum(count) as Total by src | where distinct_uri > 5
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jwalzerpitt
Influencer
01-16-2019
12:31 PM
Thx as that worked perfectly!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vnravikumar
Champion
01-16-2019
12:32 PM
welcome 🙂
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Cisco Live 2026 is almost here, and this ...
What Is the Name of the USB Key Inserted by Bob Smith? (BOTS Hint, Not the Answer)
Hello Splunkers,
So you searched, “what is the name of the usb key inserted by bob smith?”
Not gonna lie… ...
Automating Threat Operations and Threat Hunting with Recorded Future
Automating Threat Operations and Threat Hunting
with Recorded Future
June 29, 2026 | Register
Is your ...