Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Two condition match - sequential number pid an...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Need help to get following results from the search. all helps will be appreciated.
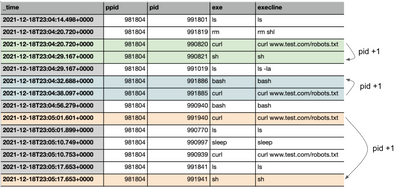
On the image below, same colors show match cases I would like to get out of my search. Here is the condition I am looking for:
Under the same pid which is all same already on image below.
example -1 ( green on the image) :
pid_of_curl = 990820
pid_of_sh = 990821
If exe = curl and ( pid_of_curl + 1 ) has exe = sh
exe is curl and 990820 + 1 = 990821 = pid in which exe = sh
if exe is either "curl" or "wget" and its pid +1 is equal to ( bash or sh ) pid
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| makeresults
| eval _raw="ppid,pid,exe
981804,991701,ls
981804,991819,rm
981804,990820,curl
981804,990821,sh
981804,991019,ls
981804,991886,bash
981804,991885,curl
981804,990940,bash
981804,991940,curl
981804,990770,ls
981804,990997,sleep
981804,990939,curl
981804,991841,ls
981804,991941,sh"
| multikv forceheader=1
| table _time ppid pid exe
| where match(exe,"curl|wget|bash|sh")
| sort 0 ppid pid
| eval curl_wget_time=if(match(exe,"curl|wget"),_time,null())
| eval bash_sh_time=if(match(exe,"bash|sh"),_time,null())
| eval curl_wget_exe=if(match(exe,"curl|wget"),exe,null())
| eval bash_sh_exe=if(match(exe,"bash|sh"),exe,null())
| eval curl_wget_pid=if(match(exe,"curl|wget"),pid,null())
| eval bash_sh_pid=if(match(exe,"bash|sh"),pid,pid+1)
| stats values(curl_wget_pid) as curl_wget_pid values(curl_wget_time) as curl_wget_time values(bash_sh_time) as bash_sh_time values(curl_wget_exe) as curl_wget_exe values(bash_sh_exe) as bash_sh_exe by ppid bash_sh_pid
| fieldformat curl_wget_time=strftime(curl_wget_time,"%F %T")
| fieldformat bash_sh_time=strftime(bash_sh_time,"%F %T")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| makeresults
| eval _raw="ppid,pid,exe
981804,991701,ls
981804,991819,rm
981804,990820,curl
981804,990821,sh
981804,991019,ls
981804,991886,bash
981804,991885,curl
981804,990940,bash
981804,991940,curl
981804,990770,ls
981804,990997,sleep
981804,990939,curl
981804,991841,ls
981804,991941,sh"
| multikv forceheader=1
| table _time ppid pid exe
| eval exe_of_interest=if(match(exe,"curl|wget|bash|sh"),pid,null())
| sort 0 ppid pid
| streamstats range(exe_of_interest) as difference window=2 by ppid
| where difference = 1 and match(exe,"bash|sh")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
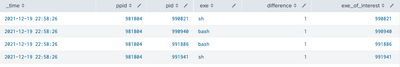
Hey @ITWhisperer
Thank you so much for spending time and providing this solution.
It gives me the following output
However, I need following matches out of the data set.
logic here is :
1. under the same ppid, (curl OR wget ) and ( bash OR sh ) should be available
2. If #1(above) is true, ((pid _of_curl + 1) OR (pid_of_wget + 1 )) = ( pid_of_sh OR pid_of_bash)
time - ppid - pid - exe
1. time2 - 981804 - 991885, 991885 - curl, bash
2. time2 -981804 - 991940, 991940 - curl, sh
Thanks again.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| makeresults
| eval _raw="ppid,pid,exe
981804,991701,ls
981804,991819,rm
981804,990820,curl
981804,990821,sh
981804,991019,ls
981804,991886,bash
981804,991885,curl
981804,990940,bash
981804,991940,curl
981804,990770,ls
981804,990997,sleep
981804,990939,curl
981804,991841,ls
981804,991941,sh"
| multikv forceheader=1
| table _time ppid pid exe
| where match(exe,"curl|wget|bash|sh")
| sort 0 ppid pid
| eval curl_wget_time=if(match(exe,"curl|wget"),_time,null())
| eval bash_sh_time=if(match(exe,"bash|sh"),_time,null())
| eval curl_wget_exe=if(match(exe,"curl|wget"),exe,null())
| eval bash_sh_exe=if(match(exe,"bash|sh"),exe,null())
| eval curl_wget_pid=if(match(exe,"curl|wget"),pid,null())
| eval bash_sh_pid=if(match(exe,"bash|sh"),pid,pid+1)
| stats values(curl_wget_pid) as curl_wget_pid values(curl_wget_time) as curl_wget_time values(bash_sh_time) as bash_sh_time values(curl_wget_exe) as curl_wget_exe values(bash_sh_exe) as bash_sh_exe by ppid bash_sh_pid
| fieldformat curl_wget_time=strftime(curl_wget_time,"%F %T")
| fieldformat bash_sh_time=strftime(bash_sh_time,"%F %T")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content