Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Splunk query for formatting the output
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk query for formatting the output
Hello,
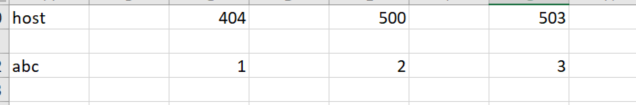
i am new to splunk and SPL. Below are the sample logs and my query. i was trying to get output like shown below picture where i need a table that contains host 404 500 503 codes but i couldn't able to figure it out. Any help would be appreciated.
index=* sourcetype=web host=ls8lw* source=access |rex field=source "/var/log/apache/(?.*).api.com-access" |rex "HTTP/1.(1|0)\" (?\d+)" | search status > 404
12.332.11.189 - - - [15/Jun/2017:19:07:35 -0400] "GET
/connections/oracle/integration/user/experienceapproval/v1/learningapprovals
HTTP/1.1" 500 273 "-" "Java/1.2.0_161"
"-" "-" 9112.13.123.134 159.112.160.51 - - [15/Jun/2017:18:14:44 -0400] "GET
/unicorn.ico HTTP/1.1" 404 800 "-"
"Mozilla/5.0 (Windows NT 6.1; WMOM64;
carpet/7.0; rv:11.0) like pecko" "-"
"-" 1125.5.125.35 48.58.788.129 - - [15/Jun/2017:17:50:05 -0400] "GET
/connections/oracle/public/user/searching/v1/Items?$filter=maxlength/itemID%20eq%20'pqwe'%20and%20searching/select=items,itemTypePD,revisionDate
HTTP/1.1" 503 77 "-"
"Apache-HttpClient/3.4 (Java 1.2
minimum; Java/1.9.0_131)" "-" "-" 198
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi iamlearner123,
see the chart command (see http://docs.splunk.com/Documentation/Splunk/7.1.1/SearchReference/Chart )
index= sourcetype=web host=ls8lw source=access
|rex field=source "yout_regex1"
|rex "your_regex2"
| where status > 404
| chart count over status BY host
Sorry for the regexes but aren't readable, use Code Sample button (101010) to show code.
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the reply ,, can i please know how to display the results only if number of errors are greater than 10. For example , if number of "500" errors count is greater than 100, then only it should display the results.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To draw a two-dimensional chart of counts like that, append ... | chart count by host status to your search. [Side note, I keep forgetting which axis is which - you might need to swap around host and status.]
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| where '500' > 10
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the reply ,, can i please know how to display the results only if number of errors are greater than 10. For example , if number of "500" errors count is greater than 100, then only it should display the results.