Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Search with Time Using a Lookup?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Search with Time Using a Lookup?
I have a lookup of hosts with a field Last_Scan_Datetime and the field values were formated using strftime(_time, "%Y-%m-%d-%H.%M.%S") . How would I go upon searching for hosts that were scanned in the last 3 days?
Everything I've found regarding searching with time has involved searching the index.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
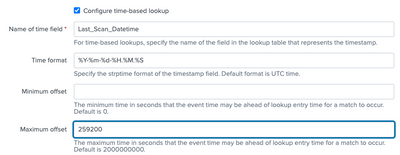
You can make a time based lookup definition where you define the settings as
Then when you search your events, assuming your host field is called host, you do
| lookup your_lookup_definition host OUTPUT Last_Scan_Datetime as found_Last_Scan_Datetime
| where isnull(found_Last_Scan_Datetime)
which will return you all the hosts where the Last_Scan_Datetime field is older than 3 days ago from the _time field in the event for that host
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Looking up times is not straightforward. For the most part, lookups do exact string matches (except for wildcard and CIDR matching, if defined). Timestamps are even trickier since Splunk can't do much with them in string format. That means something like
| inputlookup mylookup.csv where Last_Scan_Datetime > someValuewon't work. You'd have to convert the timestamp to epoch form and then compare it.
| inputlookup mylookup.csv
| eval epoch = strptime(Last_Scan_Datetime, "%Y-%m-%d-%H:%M:%S")
| where epoch > relative_time(now(), "-3d")This assumes your use case works with the inputlookup command. I know of no similar solution using lookup.
If this reply helps you, Karma would be appreciated.