Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Rename the existing Correlation search?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
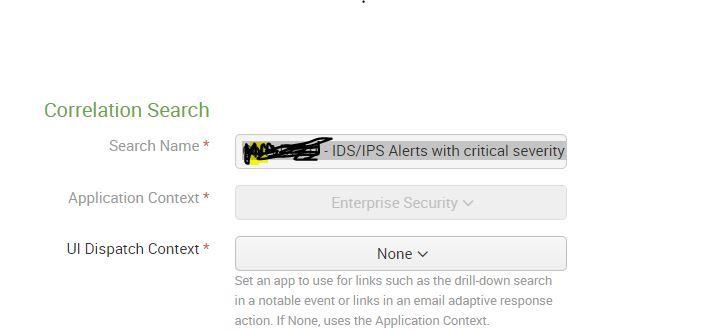
Rename the existing Correlation search?
Hi Splunkers,
Whats the best way to rename the existing correlation search.?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is an easier solution.
Click Settings > Searches,reports and alerts > search the name of the correlation
Under Actions, click Edit > Advanced Edit > and edit "action.correlationsearch.label" > Save
If you refresh the content page , it should be the new name you set it to
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
https://docs.splunk.com/Documentation/ES/5.2.1/Admin/Upgradecorrelationsearches
Upgrade correlation searches in Splunk Enterprise Security
Starting in Splunk Enterprise Security version 4.6.0, correlationsearches.conf is no longer used to define correlation searches. Instead, savedsearches.conf uniquely identifies correlation searches using the action.correlationsearch.enabled=1 parameter. The correlationsearches.conf file is deprecated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The above poster's answer does not work on the latest Enterprise Security version.
You must visit the following file
YOUR_SPLUNK_DIRECTORY/etc/apps/SplunkEnterpriseSecuritySuite/local/savedsearches.conf
Then modify two lines. I copied and pasted my config below with the parts that need to be modified in bold.
[Threat - User Failed to Login More Than 100 Times - Rule]
action.correlationsearch.enabled = 1
action.correlationsearch.label = User Failed to Login More Than 100 Times
Restart your Splunk instance after by running the following
sudo YOUR_SPLUNK_DIRECTORY/bin/splunk restart
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, they have to be renamed at the config file level because there are two configuration files involved.
Refer this link
https://answers.splunk.com/answers/138322/what-is-the-easiest-way-to-rename-a-correlation-search.htm...
steps:
cd ~/Downloads/SplunkEnterpriseSecurityInstaller/default/src/etc/apps/SA-ThreatIntelligence/default/
grep "Rule\]" savedsearches.conf
[Threat - Threat List Activity - Rule]
[Threat - Watchlisted Events - Rule]
grep "Rule\]" correlationsearches.conf
[Threat - Threat List Activity - Rule]
[Threat - Watchlisted Events - Rule]
I hope this helps you!