Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- No Results Searching Authentication.signature
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
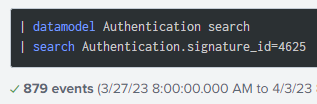
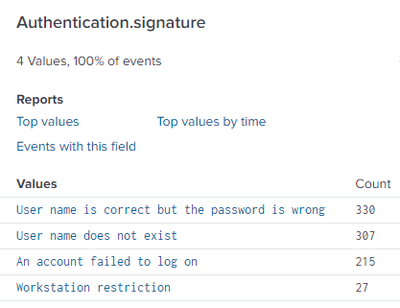
I'm trying to search in the Authentication data model for authentication attempts where the username is wrong. I get results when I search for "Authentication.signature_id=4625", and can see many "User name does not exist" events when I click on Authentication.signature in the left column.
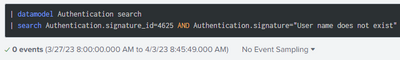
When I add " Authentication.signature="User name does not exist" " or a variation ("=*User name does not exist*", "=*exist*", etc.) I get zero results returned. Is there something I am doing wrong?
Thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I figured it out. For some reason the data model changes the signature to "User logon with misspelled or bad user account", so my searches were working but I was using terms that were not in the string. Once I changed that, I was able to find the results I was looking for.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I figured it out. For some reason the data model changes the signature to "User logon with misspelled or bad user account", so my searches were working but I was using terms that were not in the string. Once I changed that, I was able to find the results I was looking for.