Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Lookup table help
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lookup table help
tkerr357
Observer
07-01-2020
10:29 AM
Hello all,
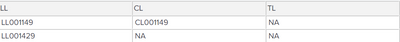
Looking for some help integrating a lookup table into my failed login search. What I am trying to achieve is to look for any events matching the base search I have below using each of the account name variations in the table. Any help is much appreciated.
base search: index=wineventlog OR index=h_wineventlog EventCode=4625 user=(LL,CL,TL would go here) | stats count by user
example of table below :
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
chrisboy68
Contributor
07-02-2020
12:32 PM
Look a inputlookup https://docs.splunk.com/Documentation/Splunk/8.0.4/SearchReference/Inputlookup
You will want to match with your base search and perform logic on the fields returned from the lookup and base.
HTH
Chris
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
tkerr357
Observer
07-07-2020
05:45 AM
sorry I have read through the documentation but can you provide a brief example of what you mean?
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Deep insights, no barriers: Splunk Observability Cloud Free Edition
As software delivery cycles continue to accelerate, observability shouldn’t be a luxury — it should be a ...
Monitoring AI Agents with Splunk Observability Cloud
Let’s say I’m running a travel planning AI app in production. A user asks for three concise hotel options in ...
[Puzzles] Solve, Learn, Repeat: Tiling
This puzzle (first published here) is based on finding groups of tessellated tiles (inspired by floor tiles I ...