Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Looking for a faster search query: Count different...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear Splunk Community,
I have the following search:
index=websphere 200 OK POST
And I have different platforms that I find like this:
index=websphere 200 OK POST LINUX
index=websphere 200 OK POST Windows
index=websphere 200 OK POST zLinux
I am currently using the following query to count all 200 OK POST events per platform:
index=websphere 200 OK POST LINUX | stats count | rename count AS "Linux" | append [search index=websphere 200 OK POST WINDOWS | stats count | rename count AS "Windows"] | append [search index=websphere 200 OK POST ZLINUX | stats count | rename count AS "zLinux"]
This is just an example, I have way more platforms that I search like in the query above. I have two issues:
- Its slow
- It counts per platform and generates table headers horizontally that I don't want
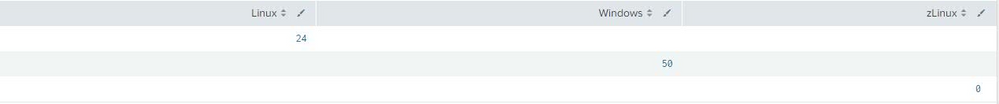
I would like to change the above so that I get the following output:
Platform | Count
Linux | 24
Windows | 50
zLinux | 0
Also, using append search seems a bit devious. There must be a simpler, faster and better way to do this, but how?
Thanks in advance
EDIT: Please note that the results are all shown in _raw , there are no platform fields or anything generated
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
index=websphere 200 OK POST (LINUX OR WINDOWS OR ZLINUX) | eval Platform=case(searchmatch("LINUX"),"LINUX", searchmatch("WINDOWS"),"WINDOWS", true(),"ZLINUX") | stats count by Platform- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
index=websphere 200 OK POST (LINUX OR WINDOWS OR ZLINUX) | eval Platform=case(searchmatch("LINUX"),"LINUX", searchmatch("WINDOWS"),"WINDOWS", true(),"ZLINUX") | stats count by Platform- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks! Works like a charm! Not familiair with searchmatch but will look into it.