Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How to use xmlkv in field extraction to identi...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to use xmlkv in field extraction to identify values in XML?
3618475
Engager
05-22-2020
12:23 PM
I have a huge XML file with many tiers. I use this command to limit the number of events for the XML data that I want to extract, then I use xmlkv to extract the XML fields. The fields that I need are extracted but not all of the data is pulled.
This is the command:
index=83261 source="service.log" sourcetype="dispatchapp" "RULE" "createMessage MsgSource" | xmlkv
This is a partial example of the XML file:
PURCHASEDLINEHAUL DISPATCH 2020-05-21T17:22:55.000Z
<ns2:numberCode>923</ns2:numberCode>
<ns2:numberType>2</ns2:numberType> </origin> <destination>
<ns2:numberCode>72</ns2:numberCode>
<ns2:numberType>2</ns2:numberType> </destination>
<purchasedCost>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>FXTR</carrier>
<vendorType>DRAY</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>923</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4022</ns2:numberCode>
</destination>
</purchasedCostTripSegment>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>BNSF</carrier>
<vendorType>RAIL</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>4022</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4040</ns2:numberCode>
</destination>
</purchasedCostTripSegment>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>NS</carrier>
<vendorType>RAIL</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>4061</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4040</ns2:numberCode>
</destination>
</purchasedCostTripSegment> </purchasedCost>
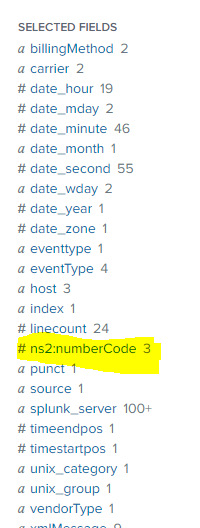
This image shows that the ns:numberCode is extracted buy only 3 but there are 5 instances in the view above. But the entire xml there are many more.
How can I get the rest of the instances in the field extraction, and how can I identify the path where these values are coming from in the XML?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
to4kawa
Ultra Champion
05-22-2020
04:43 PM
sample:
| makeresults
| eval _raw=" PURCHASEDLINEHAUL DISPATCH 2020-05-21T17:22:55.000Z
<ns2:numberCode>923</ns2:numberCode>
<ns2:numberType>2</ns2:numberType> </origin> <destination>
<ns2:numberCode>72</ns2:numberCode>
<ns2:numberType>2</ns2:numberType> </destination>
<purchasedCost>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>FXTR</carrier>
<vendorType>DRAY</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>923</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4022</ns2:numberCode>
</destination>
</purchasedCostTripSegment>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>BNSF</carrier>
<vendorType>RAIL</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>4022</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4040</ns2:numberCode>
</destination>
</purchasedCostTripSegment>
<purchasedCostTripSegment>
<purchCostReference>1587040</purchCostReference>
<carrier>NS</carrier>
<vendorType>RAIL</vendorType>
<carrierTrailerType>PZ1</carrierTrailerType>
<origin>
<ns2:numberCode>4061</ns2:numberCode>
</origin>
<destination>
<ns2:numberCode>4040</ns2:numberCode>
</destination>
</purchasedCostTripSegment> </purchasedCost>"
| multikv noheader=t
| fields _raw
| xmlkv
| rex "(?<time>\d\S+Z)"
| stats list(*) as *
You have to think about the form of the output.
Get Updates on the Splunk Community!
Splunk Observability for AI
Don’t miss out on an exciting Tech Talk on Splunk Observability for AI!Discover how Splunk’s agentic AI ...
Splunk Enterprise Security 8.x: The Essential Upgrade for Threat Detection, ...
Watch On Demand the Tech Talk on November 6 at 11AM PT, and empower your SOC to reach new heights!
Duration: ...
Splunk Observability as Code: From Zero to Dashboard
For the details on what Self-Service Observability and Observability as Code is, we have some awesome content ...