Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to sum(field) depending on another field
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello all,
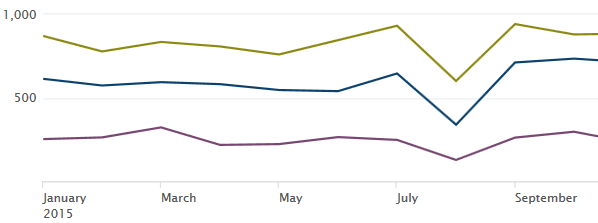
I have a field called Type with three values and I want a chart of the percentage of these three values. I am looking for a chart like this, which is easy to achieve:
But with the % value over the total count of another field for each type. I have a field called Count, that I want to sum for each type, so by now, my search is this:
| timechart sum(Count) by Type
The thing is that I cannot find a way to sum this field depending of the Type field. If I had the sum, I could calculate the percentage myself.
Someone knows if I can do it?
Thanks in advance!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
your base search | bucket span=1mon _time | stats sum(count) as count by _time Type | eventstats sum(count) as Total by _time | eval Percent=round(count*100/Total) | timechart span=1mon max(Percent) by Type
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
your base search | bucket span=1mon _time | stats sum(count) as count by _time Type | eventstats sum(count) as Total by _time | eval Percent=round(count*100/Total) | timechart span=1mon max(Percent) by Type
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
to chart of the percentage of these three values , try like :
...| top Type
or
try thi :
...| stats count by Type | eventstats sum(count) as total | eval percent = round(count/total) . " %" | fields - total
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It works! for one month, do you if there is a possibility to do it over month? as a timechart or something?
Thank you!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try like:
...|bucket _time span=1months| top Type by _time
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you so much! 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
okay, I'm approaching to it.
I need a mix of these two queries, noy I have:
on one hand:
| stats sum(Count) as suma by Type | eventstats sum(suma) as total | eval percent = round((suma/total)*100,0)."%"on the other hand:
|bucket _time span=1months| top Type by _time
Now, I need to sum the field Count for Type and moth. With this last thing you wrote me, I almost achieve it, but it counts the events and I need to sum a field for the events.
Thanks, you're helping me a lot!