Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to search for several events with one unique i...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi all,
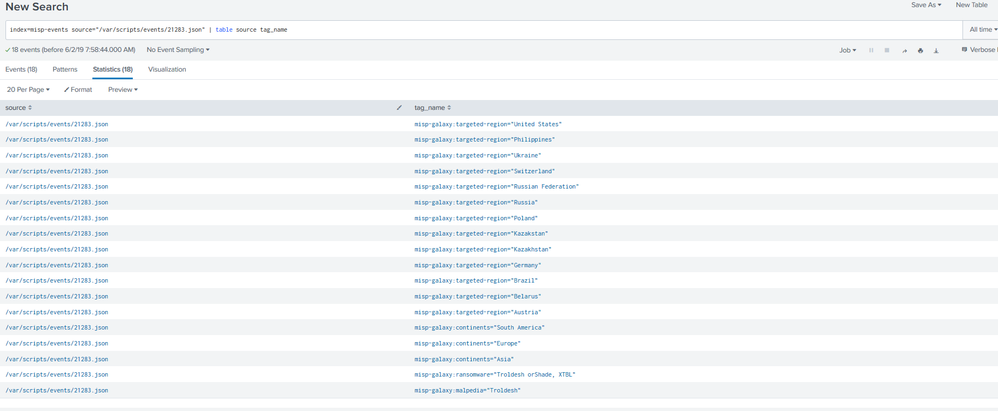
I'm trying to find a query that returns all the following tag_name with the same "source" field:
misp-galaxy:continents="Asia"
misp-galaxy:targeted-region="Russia"
misp-galaxy:ransomware="Troldesh orShade, XTBL"
The tricky part is that I have to run the search on all my source files, where the source file is actually the single-valued identifier.
What I tried was something like this:
(index=misp-events source="/var/scripts/events/*" misp-galaxy:continents="Asia") AND (index=misp-events source="/var/scripts/events/*" misp-galaxy:targeted-region="Russia") AND (index=misp-events source="/var/scripts/events/*" misp-galaxy:ransomware="Troldesh orShade, XTBL")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not sure if I understood you correctly but try this:
(index=misp-events source="/var/scripts/events/*") (misp-galaxy:continents="Asia" OR misp-galaxy:targeted-region="Russia" OR misp-galaxy:ransomware="Troldesh orShade, XTBL")
Lett me know if this doesnt help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not sure if I understood you correctly but try this:
(index=misp-events source="/var/scripts/events/*") (misp-galaxy:continents="Asia" OR misp-galaxy:targeted-region="Russia" OR misp-galaxy:ransomware="Troldesh orShade, XTBL")
Lett me know if this doesnt help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nop.
(index=misp-events source="/var/scripts/events/21283.json") (tag_name="misp-galaxy:continents="Asia"" OR tag_name="misp-galaxy:targeted-region="Russia"" OR tag_name="misp-galaxy:ransomware="Troldesh orShade, XTBL"")