Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to name with statistic/visualization?
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jialiu907
Path Finder
03-31-2023
08:36 AM
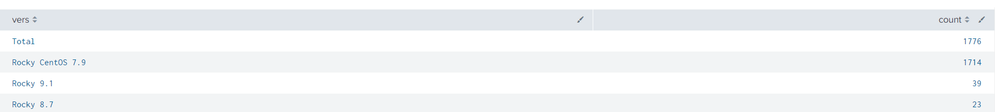
I am new to Splunk and I wanted to make a dashboard to showcase the count of Linux machines and their distributions in the environment. I have gotten the search to be almost what I want except the output statistic is wrong in the naming.
This is the current search.
index=main host=* sourcetype=syslog process=elcsend "\"config " "CentOS Linux release 7.9.2009 (Core)" OR "Rocky Linux release 8.7 (Green Obsidian)" OR "Rocky Linux release 9.1 (Blue Onyx)"
| rex "CentOS Linux release (?P<vers>\d.\d)"
| eval vers = "CentOS ".vers
| rex "Rocky Linux release (?P<vers>\d.\d)"
| eval vers = "Rocky ".vers
| dedup host
| stats count by vers
| addcoltotals label=Total labelfield=vers
| sort count desc
And this is the output.
I am looking to have "Rocky CentOS 7.9" to just be named "CentOS 7.9" while the others remain as they are.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
03-31-2023
08:58 AM
The problem stems from the vers field already having "CentOS" added and then "Rocky " is added. Try extracting separate version fields.
index=main host=* sourcetype=syslog process=elcsend "\"config " "CentOS Linux release 7.9.2009 (Core)" OR "Rocky Linux release 8.7 (Green Obsidian)" OR "Rocky Linux release 9.1 (Blue Onyx)"
| rex "CentOS Linux release (?P<vers>\d.\d)"
| rex "Rocky Linux release (?P<vers>\d.\d)"
index=main host=* sourcetype=syslog process=elcsend "\"config " "CentOS Linux release 7.9.2009 (Core)" OR "Rocky Linux release 8.7 (Green Obsidian)" OR "Rocky Linux release 9.1 (Blue Onyx)"
| rex "CentOS Linux release (?P<Cvers>\d.\d)"
| rex "Rocky Linux release (?P<Rvers>\d.\d)"
| eval Cvers = "CentOS ".Cvers
| eval Rvers = "Rocky ".Rvers
| eval vers = coalesce(Cvers, Rvers)
| dedup host
| stats count by vers
| addcoltotals label=Total labelfield=vers
| sort count desc
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
03-31-2023
08:58 AM
The problem stems from the vers field already having "CentOS" added and then "Rocky " is added. Try extracting separate version fields.
index=main host=* sourcetype=syslog process=elcsend "\"config " "CentOS Linux release 7.9.2009 (Core)" OR "Rocky Linux release 8.7 (Green Obsidian)" OR "Rocky Linux release 9.1 (Blue Onyx)"
| rex "CentOS Linux release (?P<vers>\d.\d)"
| rex "Rocky Linux release (?P<vers>\d.\d)"
index=main host=* sourcetype=syslog process=elcsend "\"config " "CentOS Linux release 7.9.2009 (Core)" OR "Rocky Linux release 8.7 (Green Obsidian)" OR "Rocky Linux release 9.1 (Blue Onyx)"
| rex "CentOS Linux release (?P<Cvers>\d.\d)"
| rex "Rocky Linux release (?P<Rvers>\d.\d)"
| eval Cvers = "CentOS ".Cvers
| eval Rvers = "Rocky ".Rvers
| eval vers = coalesce(Cvers, Rvers)
| dedup host
| stats count by vers
| addcoltotals label=Total labelfield=vers
| sort count desc
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
SOK it to Me: Top 3 Benefits of Using Splunk Operator on Kubernetes that’ll Make ...
Thursday, July 9, 2026 | 11:00AM–12:00PM PDT
Duration: 1 hour (includes Q&A)
Managing can feel like a ...
Upgrade Prep for 10.4, Network Observability Deep Dives, and More from Splunk Lantern
Splunk Lantern is Splunk’s customer success center that provides practical guidance from Splunk experts on key ...
Splunk Developer Day announcements: AI agents, MCP tools, Forecasting, and Custom ...
Splunk Developer Day was packed with product and platform updates for developers building in the AI ...