Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to extract the field with regex
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
danielwan
Explorer
09-25-2017
06:42 PM
I would like to extract the field of "/home/y/conf/video_dir.conf" with regex when the event contains "critical" keyword (there are some other state keywords like "normal", "debug")
2011-01-01 01:49:00 UTC [ critical] [ PID=14154][ GENERAL] File /home/y/conf/video_dir.conf doesn't exist or not readable.
I ran '... | rex field=_raw "^.critical.*File\s+(?)\s+.$" but it's not working. Any advice on making it work?
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
09-25-2017
11:48 PM
Please try -
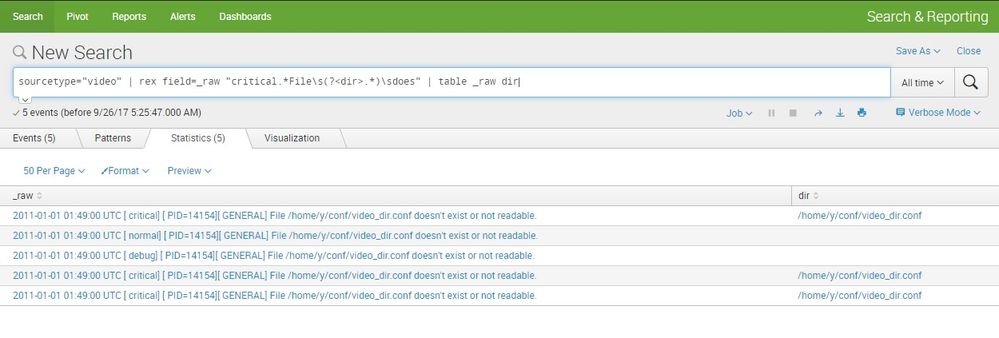
sourcetype="video" | rex field=_raw "critical.*File\s(?<dir>.*)\sdoes" | table _raw dir
thanks and best regards,
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
inventsekar

SplunkTrust
09-25-2017
11:48 PM
Get Updates on the Splunk Community!
Data Management Digest – December 2025
Welcome to the December edition of Data Management Digest!
As we continue our journey of data innovation, the ...
Index This | What is broken 80% of the time by February?
December 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...
Unlock Faster Time-to-Value on Edge and Ingest Processor with New SPL2 Pipeline ...
Hello Splunk Community,
We're thrilled to share an exciting update that will help you manage your data more ...