Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Exacting info from nested data with specific p...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
paulito
Explorer
04-13-2022
10:53 AM
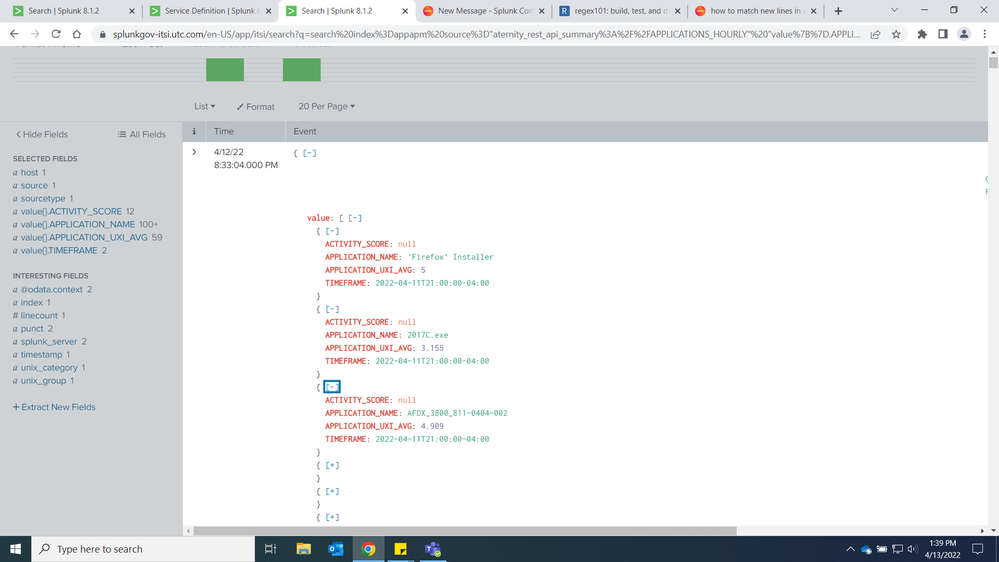
I need to extract the Activity Score and Application UXI Average but only when the Application Name is a certain name.
It's a weird one for me because of the way data comes in. As you can see each event has multiple application names, activity scores, uxi averages and timeframes. So even when I specify for a certain app in a search, since the app name is in an event, I get the whole event which includes all the other apps and metrics.
I hope what I'm explaining is clear and any help would be appreciated.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ITWhisperer

SplunkTrust
04-13-2022
11:45 AM
| spath value{} output=value
| mvexpand value
| spath input=value
| where APPLICATION_NAME="certain app"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ITWhisperer

SplunkTrust
04-13-2022
11:45 AM
| spath value{} output=value
| mvexpand value
| spath input=value
| where APPLICATION_NAME="certain app"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
paulito
Explorer
04-13-2022
12:23 PM
Works perfectly, thank you!
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Agent Mode Engaged! Enchaining Agentic Operations with Splunk AI Assistant 2.0
Are you ready to transform how your team handles complex data requests?
We invite you to our upcoming ...
Announcing Modern Navigation: A New Era of Splunk User Experience
We are excited to introduce the Modern Navigation feature in the Splunk Platform, available to both cloud and ...
Modernize your Splunk Apps – Introducing Python 3.13 in Splunk
We are excited to announce that the upcoming releases of Splunk Enterprise 10.2.x and Splunk Cloud Platform ...