Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Extracting desired data from search result
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to extract desired data from search result?
sneha03
New Member
05-11-2022
05:04 AM
Hi Team,
We are trying below search:
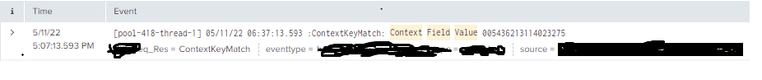
index=index_123 host=xyz source="/sys_apps_01/pqr/logs/xyz/mapper_xyz.log" ContextKeyMatch: Context Field Value
which gives below results with multiple rows as below:
Now we want to extract data after Context Filed Value. The string having "Context Filed Value" is of variable string length
We have multiple rows like above and we need to extract such data from each row. like : 005436213114023275.
Once we have the extracted data we need to fetch only last 12 digits
Could you please suggest regarding this?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ITWhisperer

SplunkTrust
05-11-2022
05:15 AM
Try something like this
| rex "Context Field Value\s+\d*(?<value>\d{12})"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
PickleRick

SplunkTrust
05-11-2022
05:15 AM
Ideally, you should have this defined as an automatically extracted field so you don't have to do it ad-hoc every time. But for a one-off extraction you can do it with the rex command. Something like this:
<your search>
| rex "Context Filed Value.*(?<my_field>\d{12})$"
Get Updates on the Splunk Community!
Observe and Secure All Apps with Splunk
Join Us for Our Next Tech Talk: Observe and Secure All Apps with SplunkAs organizations continue to innovate ...
Splunk Decoded: Business Transactions vs Business IQ
It’s the morning of Black Friday, and your e-commerce site is handling 10x normal traffic. Orders are flowing, ...
Fastest way to demo Observability
I’ve been having a lot of fun learning about Kubernetes and Observability. I set myself an interesting ...