Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to edit my search to find Fortinet Internet Br...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to edit my search to find Fortinet Internet Browsing Time by User per Day?
We have Fortinet FSSO in place and we have syslogs coming into Splunk. I need a way to report how much time users are spending on the Internet.
The rule below which is not providing accurate results for us. I narrowed my search window down to one day and for one user the result was: 13:57:59 and another user 05:27:38. Both users work an 8 hour shift. Also, when I run this against other users, most of them come back with approx. a full 7-8 hours of browsing time, which would be their entire shift. This was tested on users who are not spending nearly that much time actively browsing the Internet.
<usernamehere> | transaction user maxpause=5m | stats sum(duration) as browsing_time by user | sort -browsing_time | head 10 | fieldformat browsing_time = tostring(browsing_time,"duration")
Can someone help me either craft the proper rule. I understand it may not be 100% accurate due to Fortinet FSSO agent timeout/idle settings, but I need approximates.
Thank you in advance,
Lee
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@DalJeanis,
I have done this sort of testing with select users already. It appears that if the Fortinet FSSO agent doesn't log them out after idle limit, then they're counted as continued browse time. However, I could be wrong... I am not expecting exact cumulative browse time duration, but an approx. would be nice instead of the numbers that are way off.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
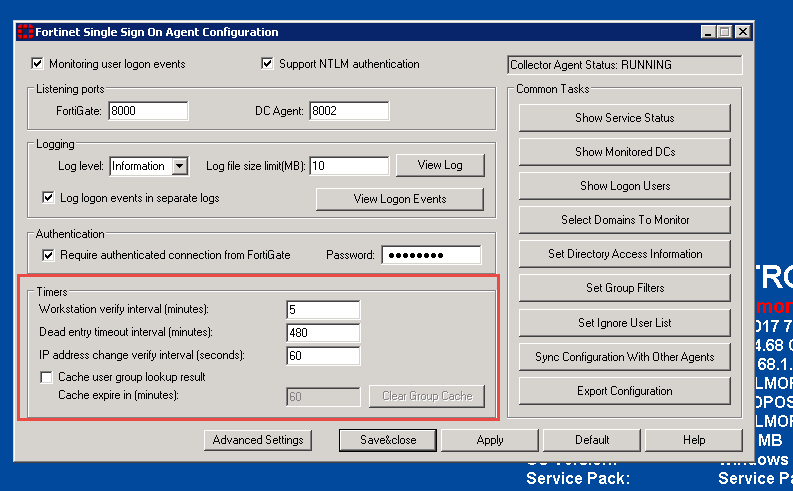
That's your 480 in dead interval timeout. If Fortinet cannot contact the workstation for that long, it will end the session. (Not necessarily forcing an actual logout/logon at that point, but just sort of "forgetting" about it. Lots of background info in this thread... https://forum.fortinet.com/tm.aspx?m=119045)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@DAlJeanis,
Thanks for the reply, yes there is alot of moving parts with this issue. I didn't think my FSSO agent was miss-configured, but I want to rule that out.
I should be able to get realistic results in the above Splunk rule against my Fortinet syslogs. The data doesn't even make sense and essentially states the user is browsing "actively" all day...
Anyone else have ideas on how I can
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk can only report on the events that it is sent. Fortinet is not necessarily misconfigured, it is just configured in a way that is not raising the information that you would like to report on.
It may be that the feasible way to get what you want is to use the Fortinet information to identify who, and use other DNS or proxy data to identify when and how long.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The basic issue with such a search is that nowadays browsers do things constantly all by themselves. For instance, any news page will generally be rotating stories and updating headline banners, and so on, whether the browser is being used, or is sitting minimized on the desktop.
I was stunned the other day when I found that my own browsing in a single day of splunk research had accessed (or been denied) literally thousands of files on the Internet, and hundreds of the accesses occurred during the time that I was at lunch.
You are going to have to differentiate somehow between different types of files, and eliminate all the various autoplay media and tracking tags and such that complicate the story.
My suggestion is to take some volunteer users, have them browse the internet for 15-20 minutes, then have them minimize the browser (or not) and go to lunch for the next hour. Review the kinds of files that are hit during the idle time, and focus on the kinds that indicate active participation. It may be that the number of files retrieved per second is a decent proxy for active participation. More likely you are going to have to filter both by file type and by domain category to get an approximate weighting.